Security agents promise to make cybersecurity simple – install one solution and protect your entire digital world. This approach appeals to businesses and IT teams who want comprehensive protection without the complexity of managing multiple security tools.
This guide is for IT professionals, security managers, and business leaders who need to understand whether convenient security solutions actually deliver the protection they promise.
Modern security software convenience comes with hidden costs that many organizations don’t discover until it’s too late. The most user-friendly security agents often create significant endpoint security vulnerabilities while appearing to provide complete coverage.
We’ll explore how convenient security solutions can create blind spots in your defense strategy, the real security challenges that single-agent approaches frequently miss, and practical steps to balance usability with genuine protection. You’ll learn to spot the difference between security that feels comprehensive and security that actually works when attacks happen.
The security software trade-offs you make today determine whether your organization stays protected or becomes the next breach headline.
Understanding Security Agents and Their Appeal

What Security Agents Are and How They Work
Security agents are software programs that run continuously on devices to monitor, detect, and respond to cyber threats. These endpoint security solutions work as digital bodyguards, scanning files, monitoring network traffic, and analyzing system behavior for suspicious activities. Modern security agents use artificial intelligence and machine learning to identify malware, prevent data breaches, and automatically quarantine threats before they can cause damage.
Why Users Gravitate Toward Automated Security Solutions
Businesses and individuals choose security software convenience because manual threat detection requires extensive cybersecurity expertise that most organizations lack. Automated security solutions promise round-the-clock protection without requiring dedicated security teams or constant user intervention. The appeal lies in having enterprise-grade security that works silently in the background, allowing users to focus on their core activities while the agent handles potential threats.
The Promise of Effortless Protection
Convenient security solutions market themselves as comprehensive shields that eliminate the need for security knowledge or active management. Vendors promote these tools as “set-and-forget” solutions that provide complete protection through automation alone. This promise of effortless security appeals especially to small businesses and non-technical users who want robust cybersecurity protection without the complexity of managing multiple security tools or understanding technical security concepts.
The Convenience Factor That Drives Adoption
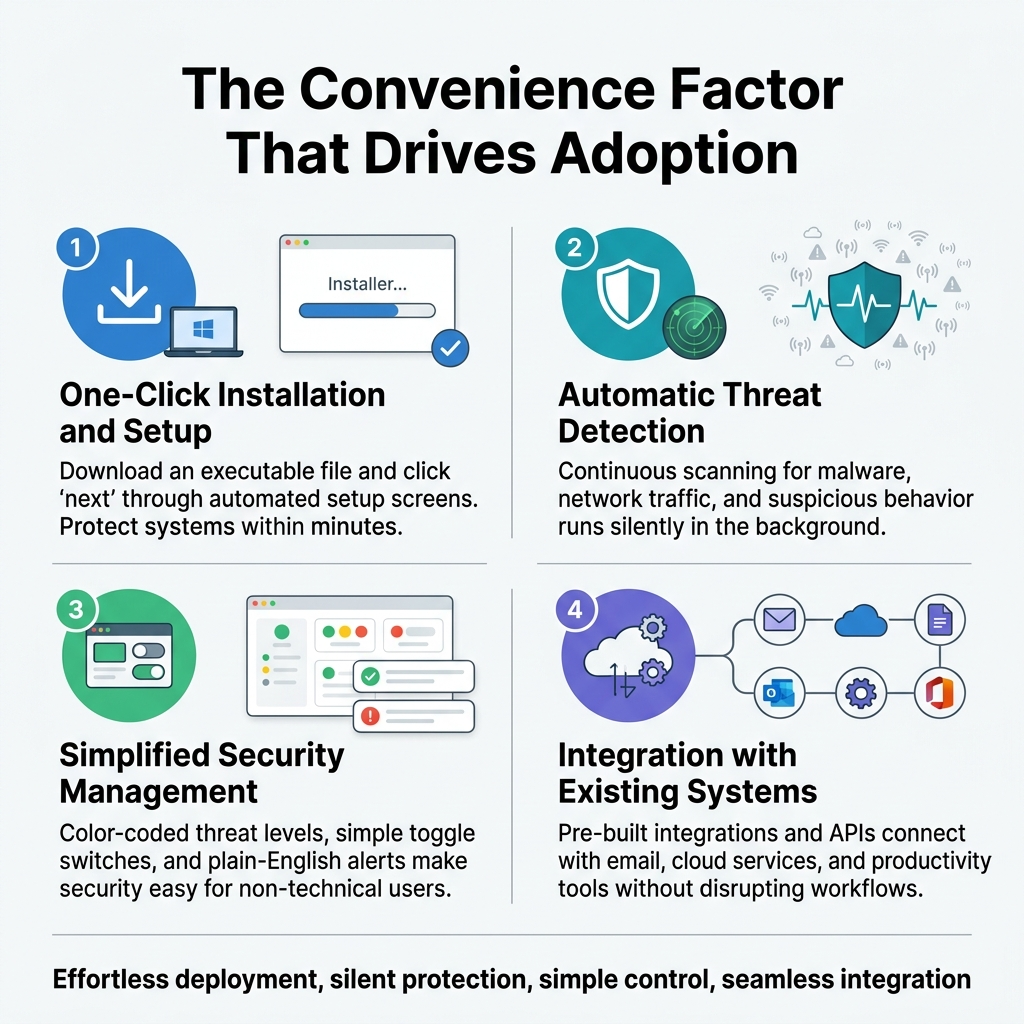
One-Click Installation and Setup Process
Modern security agents promise effortless deployment through streamlined installation wizards that eliminate technical barriers. Users can protect their systems within minutes, often requiring nothing more than downloading an executable file and clicking “next” through automated setup screens. This approach removes the complexity traditionally associated with enterprise security software, making robust protection accessible to organizations without dedicated IT teams.
Automatic Threat Detection Without User Intervention
Security software convenience reaches its peak with hands-off threat detection that operates silently in the background. These convenient security solutions continuously scan for malware, monitor network traffic, and analyze suspicious behavior patterns without disrupting daily workflows. Users appreciate this set-and-forget approach, as it provides peace of mind while requiring minimal technical knowledge or ongoing maintenance from busy professionals.
Simplified Security Management for Non-Technical Users
Dashboard interfaces in modern security agents transform complex cybersecurity data into digestible visual summaries that anyone can understand. Color-coded threat levels, simple toggle switches for security features, and plain-English alerts replace intimidating technical jargon that once intimidated non-technical users. This democratization of security management allows small businesses and individual users to maintain strong defenses without hiring specialized cybersecurity personnel.
Integration with Existing Systems and Workflows
Today’s security agents seamlessly connect with popular business applications, cloud services, and operating systems through pre-built integrations and APIs. They automatically sync with email platforms, file sharing services, and productivity suites to provide comprehensive protection without forcing users to abandon familiar tools. This compatibility reduces friction during adoption and ensures that security measures enhance rather than hinder existing business processes.
Hidden Vulnerabilities in Convenient Security Solutions

False Sense of Security Creates Risky User Behavior
When users install convenient security solutions, they often develop a dangerous overconfidence in their digital safety. This false sense of security leads to riskier online behavior – clicking suspicious links, downloading questionable files, or sharing sensitive information more freely. Security agents that promise comprehensive protection with minimal user input can actually increase vulnerability by making people less cautious about potential threats.
Over-Reliance on Single Security Layer Protection
Most convenient security solutions operate as a single point of defense, creating critical vulnerabilities in enterprise environments. When organizations depend solely on endpoint security agents without implementing additional layers like network monitoring or user training, they leave significant gaps in their defense strategy. Cybercriminals actively target these single-layer approaches, knowing that bypassing one security agent often grants complete system access.
Limited Customization Reduces Effectiveness
Convenient security software typically offers minimal customization options to maintain simplicity, but this approach severely limits protection effectiveness. Organizations with unique security requirements or specialized environments find themselves constrained by one-size-fits-all solutions that can’t adapt to their specific threat landscape. The trade-off between convenience and customization often leaves critical assets exposed to targeted attacks that exploit these configuration limitations.
Real Security Challenges That Agents Often Miss

Advanced Persistent Threats That Bypass Automated Detection
Security agents excel at catching known threats but struggle with sophisticated attackers who design campaigns specifically to evade automated systems. APTs use living-off-the-land techniques, legitimate tools, and patient reconnaissance to establish footholds that security software simply can’t recognize as malicious. These attacks move laterally through networks using authorized credentials and standard protocols, making detection incredibly challenging for endpoint security vulnerabilities.
Social Engineering Attacks Targeting Human Psychology
Automated security agents can’t protect against human manipulation, which remains cybercriminals’ favorite attack vector. Phishing emails, pretexting calls, and psychological manipulation bypass technical controls entirely by targeting employees directly. Security software trade-offs become apparent when attackers use legitimate communication channels and trusted relationships to gain access, rendering even the most sophisticated security agents powerless against basic human psychology.
Zero-Day Exploits and Novel Attack Vectors
Security agents rely heavily on signature-based detection and behavioral patterns, leaving organizations vulnerable to completely new attack methods. Zero-day exploits target unknown vulnerabilities that haven’t been patched or documented, while novel attack vectors use emerging technologies in unexpected ways. Real security protection requires adaptive defenses that can respond to threats that don’t match any existing security agent limitations or predefined rules.
Insider Threats That Appear as Legitimate Activity
Malicious insiders pose unique challenges because their activities look completely normal to security software. These threats use authorized access, work during regular hours, and perform actions within their job scope while stealing data or sabotaging systems. Enterprise security solutions struggle to differentiate between legitimate business activities and insider threats, especially when the malicious actor understands exactly how security agents monitor and flag suspicious behavior patterns.
Finding the Right Balance for Maximum Protection
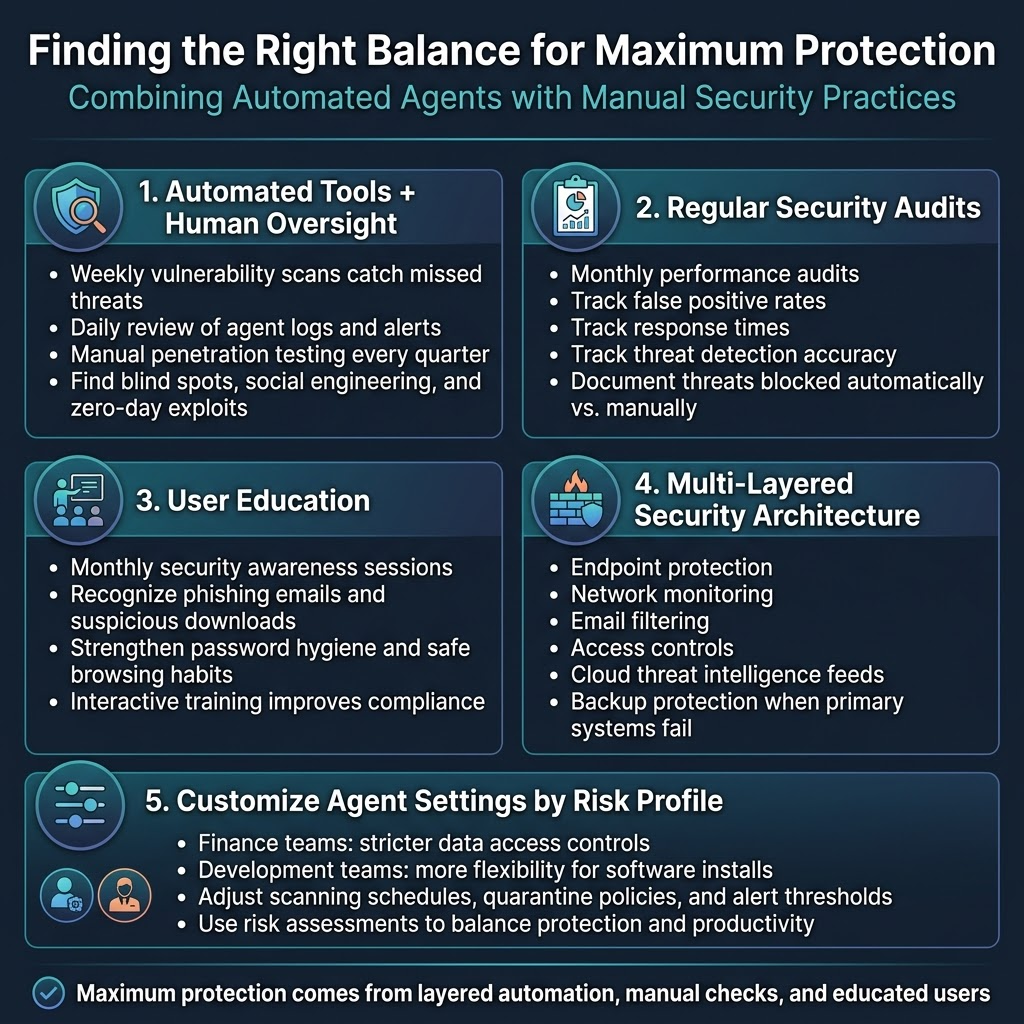
Combining Automated Agents with Manual Security Practices
Security agents work best when paired with human oversight and regular manual checks. Smart organizations run weekly vulnerability scans alongside their automated tools, catching threats that agents might miss. Security teams should schedule daily reviews of agent logs and alerts, looking for patterns that suggest sophisticated attacks or configuration gaps.
Manual penetration testing every quarter reveals blind spots in automated protection. Expert analysts can spot social engineering attempts and zero-day exploits that even advanced security software struggles to identify, creating a robust defense strategy.
Regular Security Audits and Agent Performance Reviews
Monthly performance audits help identify when security agents become outdated or misconfigured. Track key metrics like false positive rates, response times, and threat detection accuracy to measure real security protection effectiveness. Document which threats your current agents successfully block versus those requiring manual intervention.
Annual reviews should evaluate whether your security software convenience actually compromises protection levels. Compare agent performance against industry benchmarks and emerging cybersecurity vs convenience trade-offs to ensure maximum enterprise security.
User Education to Complement Automated Protection
Employee training bridges critical gaps that automated systems can’t fill alone. Monthly security awareness sessions teach staff to recognize phishing emails, suspicious downloads, and social engineering tactics that slip past endpoint security vulnerabilities. Regular workshops on password hygiene and safe browsing habits strengthen your human firewall.
Interactive training modules help employees understand why certain security protocols exist, increasing compliance with convenient security solutions. When users grasp the reasoning behind security measures, they’re more likely to follow procedures even when agents aren’t actively monitoring.
Multi-Layered Security Architecture Implementation
Effective protection requires multiple overlapping security layers rather than relying solely on single-point solutions. Deploy endpoint protection, network monitoring, email filtering, and access controls that work together to catch different attack vectors. Each layer should complement rather than duplicate the others’ capabilities.
Cloud-based threat intelligence feeds enhance on-premises security agents with real-time attack signatures and behavioral analytics. This layered approach addresses security agent limitations by ensuring backup protection when primary systems fail or miss sophisticated threats targeting enterprise environments.
Customizing Agent Settings for Specific Risk Profiles
Different departments face unique security challenges requiring tailored agent configurations. Finance teams need stricter controls around financial data access, while development teams require more flexibility for legitimate software installations. Customize scanning schedules, quarantine policies, and alert thresholds based on each group’s actual risk exposure.
Regular risk assessments help fine-tune these security software trade-offs for optimal protection without hampering productivity. Adjust agent sensitivity levels based on user behavior patterns, ensuring high-risk users receive enhanced monitoring while maintaining usability for standard operations.

Security agents promise to make our digital lives easier, but this convenience often comes at a hidden cost. While these tools excel at handling routine tasks and providing quick fixes, they frequently miss the deeper security challenges that truly matter. The appeal is obvious – who wouldn’t want automated protection that works in the background? Yet this same automation can create blind spots, leaving users vulnerable to sophisticated threats that require human judgment and critical thinking.
The key isn’t choosing between convenience and security, but finding smart ways to combine both. Use security agents for what they do best: managing repetitive tasks and catching obvious threats. But don’t let them replace your own security awareness and decision-making. Stay involved in your digital protection, question unusual activities, and remember that the most secure approach often involves multiple layers of defense. Your security is too important to leave entirely in the hands of any single solution, no matter how convenient it claims to be.