Managing AWS Secrets Manager backup across multiple AWS accounts presents unique security and operational challenges that enterprise teams face daily. When your organization spans dozens of accounts, protecting sensitive data like API keys, database passwords, and certificates requires a robust multi-account AWS architecture that balances security with accessibility.
This guide is designed for DevOps engineers, security architects, and cloud administrators who need to implement enterprise AWS secrets architecture at scale. Whether you’re managing a growing startup’s cloud infrastructure or overseeing an enterprise’s complex multi-account setup, you’ll learn how to build resilient systems that keep your secrets safe while enabling smooth operations.
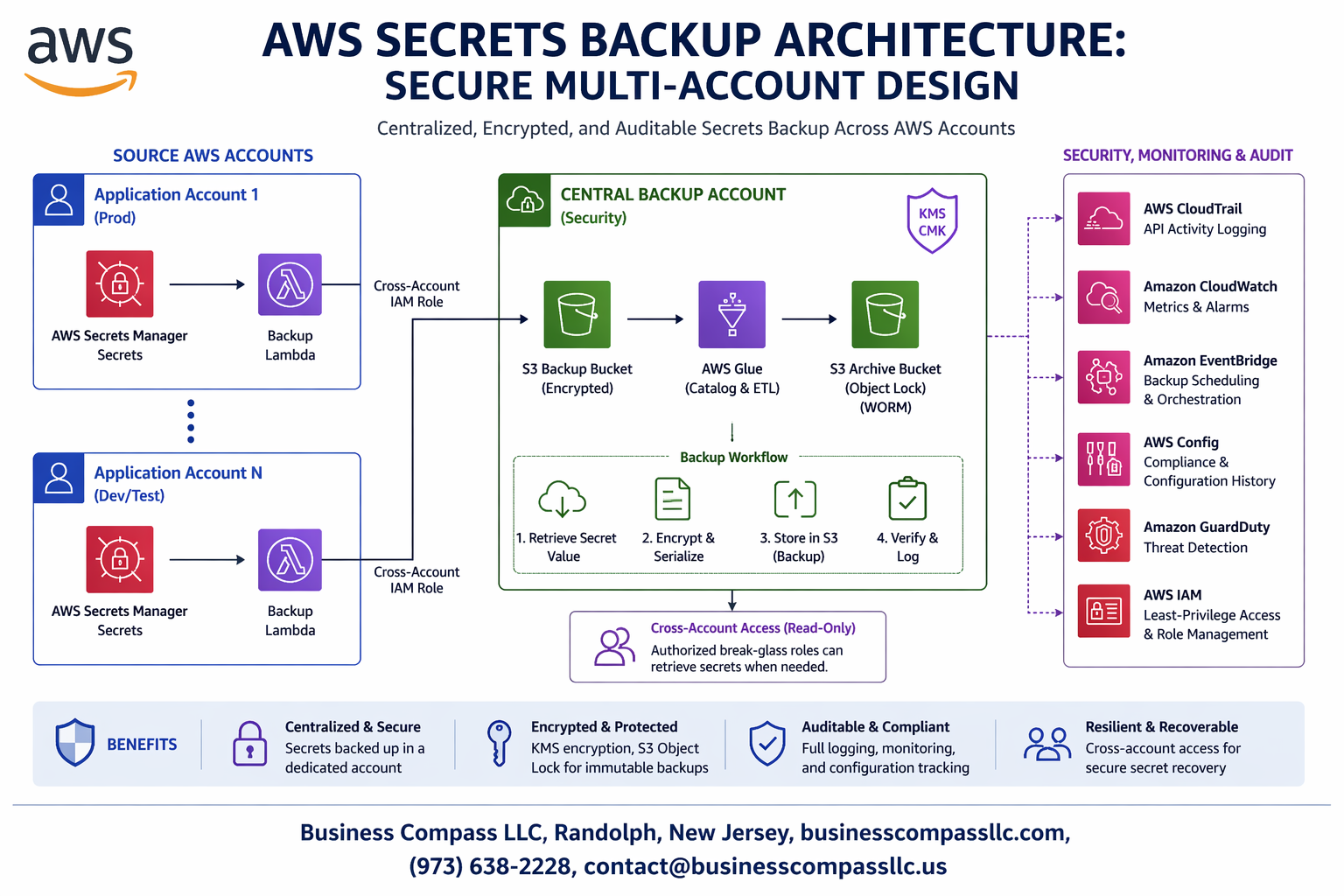
We’ll walk through designing secure multi-account design AWS patterns that protect your critical secrets, implementing cross-account secrets access control that follows the principle of least privilege, and building comprehensive AWS secrets disaster recovery processes that ensure business continuity. You’ll also discover AWS secrets management best practices for monitoring and auditing that help you maintain compliance while detecting potential security threats across your entire organization.
Understanding AWS Secrets Management Challenges in Multi-Account Environments

Critical security risks of scattered secrets across accounts
When organizations distribute secrets randomly across multiple AWS accounts without proper oversight, they create dangerous security blind spots that attackers can exploit. Each isolated secret becomes a potential entry point, and without centralized AWS secrets management best practices, security teams lose visibility into who accesses what credentials and when. This fragmentation makes it nearly impossible to rotate credentials systematically or detect suspicious access patterns across your enterprise AWS secrets architecture.
The lack of standardized secret handling creates inconsistent security policies where some accounts might have weak encryption while others lack proper access controls. Teams often resort to sharing secrets through insecure channels like email or Slack, completely bypassing AWS Secrets Manager backup protocols and exposing sensitive data to interception.
Compliance requirements for centralized secret governance
Regulatory frameworks like SOX, HIPAA, and PCI DSS demand strict controls over how organizations handle sensitive credentials and API keys. Auditors expect clear documentation showing who accessed secrets, when changes occurred, and how organizations protect data at rest and in transit. Multi-account AWS architecture without proper governance makes these compliance requirements extremely challenging to meet.
Companies face significant penalties when they can’t demonstrate proper secret lifecycle management or fail to show adequate separation of duties. Centralized governance through AWS Secrets Manager backup strategies enables automated compliance reporting and ensures consistent security policies across all accounts.
Operational complexity of managing secrets at scale
Managing hundreds or thousands of secrets across dozens of AWS accounts quickly becomes a nightmare without proper automation and cross-account secrets access control. Development teams waste hours hunting down the right credentials, while operations teams struggle to update secrets without breaking production systems. Manual secret rotation becomes virtually impossible at enterprise scale.
Different teams often implement their own secret management solutions, creating a patchwork of incompatible systems that don’t communicate with each other. This fragmentation slows down deployment pipelines and increases the risk of using outdated or compromised credentials in production environments.
Cost implications of inefficient secret distribution
Poor secret management practices directly impact your AWS bill through inefficient resource usage and duplicated storage costs. When teams can’t easily share secrets across accounts, they often create multiple copies of the same credentials, leading to unnecessary AWS Secrets Manager charges. Emergency credential updates require manual intervention across multiple accounts, consuming valuable engineering time that could be spent on revenue-generating activities.
Organizations also face hidden costs from security incidents caused by compromised secrets, including incident response time, system downtime, and potential regulatory fines. Implementing secure multi-account design AWS from the start prevents these expensive security breaches and reduces long-term operational overhead.
Core Components of Secure AWS Secrets Backup Architecture

AWS Secrets Manager as the primary secret store
AWS Secrets Manager serves as the backbone of enterprise secrets management, providing centralized storage with automatic rotation capabilities. This managed service eliminates the security risks of hardcoded credentials while offering seamless integration across your multi-account AWS architecture. The service encrypts secrets at rest and in transit, ensuring your sensitive data remains protected throughout its lifecycle.
Cross-account IAM roles for secure access control
Cross-account IAM roles enable secure secrets access without sharing long-term credentials between accounts. These roles use temporary security tokens with precise permissions, following the principle of least privilege. By establishing trust relationships between accounts, organizations can maintain strict access controls while enabling necessary cross-account functionality for their AWS secrets management best practices.
AWS KMS encryption keys for end-to-end protection
KMS customer-managed keys provide granular control over encryption operations and access policies for your secrets backup strategy. Each account can maintain its own encryption keys or share keys across accounts based on security requirements. Key rotation, audit trails, and fine-grained permissions ensure comprehensive protection for your multi-account AWS architecture while maintaining compliance with enterprise security standards.
Designing Multi-Account Secret Distribution Strategies

Hub-and-spoke model for centralized secret management
The hub-and-spoke architecture creates a single source of truth for secrets management across your AWS organization. Your central hub account stores and manages all primary secrets using AWS Secrets Manager, while spoke accounts consume these secrets through cross-account IAM roles and policies. This centralized approach simplifies secret lifecycle management, reduces operational overhead, and ensures consistent security policies across all environments.
Cross-account resource sharing enables spoke accounts to access secrets without duplicating sensitive data. The hub maintains master copies of database credentials, API keys, and certificates, automatically distributing updates to dependent accounts through AWS Resource Access Manager (RAM) or direct cross-account permissions.
Regional replication for disaster recovery and performance
Multi-region secret replication ensures business continuity and reduces latency for geographically distributed applications. AWS Secrets Manager’s built-in cross-region replication automatically maintains synchronized copies of your secrets across multiple AWS regions, providing seamless failover capabilities during regional outages.
Performance optimization comes from strategic regional placement – storing secrets closer to consuming applications reduces network latency and improves response times. Configure automatic failover mechanisms using Route 53 health checks and Application Load Balancer routing to redirect traffic when primary regions become unavailable.
Account isolation patterns for enhanced security boundaries
Security boundaries strengthen when secrets remain isolated within specific account contexts based on environment types or business units. Production secrets stay completely separated from development environments through dedicated account structures, preventing accidental exposure or unauthorized access between different operational contexts.
Implement least-privilege access patterns using account-specific IAM policies and cross-account trust relationships. Each account maintains its own secret namespace while central governance policies enforce consistent naming conventions, encryption standards, and access logging requirements across the entire multi-account AWS architecture.
Automated secret rotation across multiple environments
Automated rotation workflows ensure secrets remain fresh across all connected accounts and environments simultaneously. Lambda functions orchestrate rotation schedules, updating database passwords, API tokens, and certificates while coordinating changes across dependent systems through AWS Step Functions and EventBridge notifications.
Environment-specific rotation policies accommodate different security requirements – production secrets might rotate monthly while development environments update weekly. AWS Systems Manager Parameter Store integration enables seamless coordination between Secrets Manager and application configuration, automatically triggering deployments when secret values change.
Implementing Cross-Account Access Controls and Permissions

Resource-based policies for granular secret sharing
Resource-based policies in AWS Secrets Manager provide direct control over who can access specific secrets across different AWS accounts. These policies attach directly to secrets and define precise permissions without requiring complex cross-account IAM role assumptions. By setting conditions based on source IP, time of day, or MFA requirements, organizations can create fine-grained access controls that align with their security requirements while maintaining operational flexibility across multi-account environments.
Least privilege access principles for service accounts
Service accounts should receive only the minimum permissions necessary for their specific functions within the AWS secrets backup strategy. Cross-account secrets access control works best when each service account has clearly defined scopes, preventing unnecessary exposure of sensitive data. Regular permission audits and automated policy reviews help maintain this principle as your multi-account AWS architecture evolves and new services require secret access.
Temporary credential mechanisms using AWS STS
AWS Security Token Service (STS) enables secure temporary access to secrets without permanent cross-account permissions. AssumeRole operations create time-limited credentials that service accounts can use to retrieve secrets from backup locations during disaster recovery scenarios. This approach reduces the attack surface by eliminating long-lived credentials while providing the flexibility needed for automated backup processes and emergency access patterns in enterprise AWS secrets architecture deployments.
Backup and Recovery Mechanisms for Business Continuity

Automated backup scheduling with AWS Lambda
AWS Lambda functions serve as the backbone for automated AWS Secrets Manager backup workflows, executing on customizable schedules through CloudWatch Events. These serverless functions can retrieve secrets across multiple accounts, encrypt backup data using customer-managed KMS keys, and store copies in designated S3 buckets with proper versioning enabled.
Cross-region replication for geographic redundancy
Geographic distribution of secrets backups protects against regional outages and meets compliance requirements for data residency. AWS Secrets Manager’s native cross-region replication automatically synchronizes secret versions to secondary regions, while custom Lambda functions can replicate to additional regions based on business needs. This multi-region approach ensures secrets remain accessible during disaster scenarios.
Point-in-time recovery capabilities for critical secrets
Secret versioning in AWS Secrets Manager maintains historical copies of credential updates, enabling recovery to specific timestamps when corruption or unauthorized changes occur. Organizations can implement retention policies through lifecycle management rules, automatically archiving older versions to cost-effective storage tiers while maintaining immediate access to recent versions for rapid restoration.
Disaster recovery testing and validation procedures
Regular disaster recovery drills validate backup integrity and recovery procedures across all account environments. Automated testing scripts should verify secret accessibility, cross-account permissions, and restoration timeframes quarterly. These validation procedures must include failover scenarios where primary regions become unavailable, ensuring backup mechanisms function correctly when needed most for business continuity.
Monitoring and Auditing Secret Access Across Accounts

CloudTrail integration for comprehensive audit logging
AWS CloudTrail serves as the backbone for AWS secrets monitoring and auditing across your multi-account architecture. Every API call to AWS Secrets Manager gets captured, including secret retrieval, rotation events, and permission changes. Configure CloudTrail in each account with cross-account delivery to a centralized logging bucket, enabling complete visibility into secret access patterns. The integration captures critical metadata like user identity, source IP addresses, and timestamps, creating an immutable audit trail that supports enterprise AWS secrets architecture compliance requirements.
Real-time alerting for unauthorized access attempts
CloudWatch Events combined with Lambda functions can detect suspicious secret access patterns instantly. Set up alerts for unusual access times, unknown IP addresses, or rapid secret retrievals that might indicate compromised credentials. Configure SNS notifications to security teams when secrets are accessed outside normal business hours or from unexpected geographic locations. These real-time monitoring capabilities strengthen your AWS secrets management best practices by enabling immediate response to potential security incidents before they escalate.
Compliance reporting and governance dashboards
Build comprehensive dashboards using CloudWatch and third-party tools to visualize secret access metrics across your multi-account AWS architecture. Track key indicators like secret rotation frequency, failed access attempts, and cross-account permissions usage. Generate automated compliance reports that demonstrate adherence to security policies and regulatory requirements. These governance tools help validate your AWS secrets backup strategy effectiveness while providing executives with clear visibility into organizational security posture and risk management practices.

Managing secrets across multiple AWS accounts doesn’t have to be a security nightmare. The architecture patterns we’ve covered – from centralized secret distribution to cross-account access controls – give you the foundation to keep your sensitive data both secure and accessible. When you combine proper backup mechanisms with solid monitoring and auditing practices, you create a system that can handle both everyday operations and disaster scenarios with confidence.
Start small by implementing cross-account access controls for your most critical secrets, then gradually expand your backup and monitoring coverage. Your future self will thank you when an outage hits and your recovery process runs smoothly because you took the time to design it right. Remember, good secrets management isn’t just about security – it’s about making sure your applications keep running when it matters most.