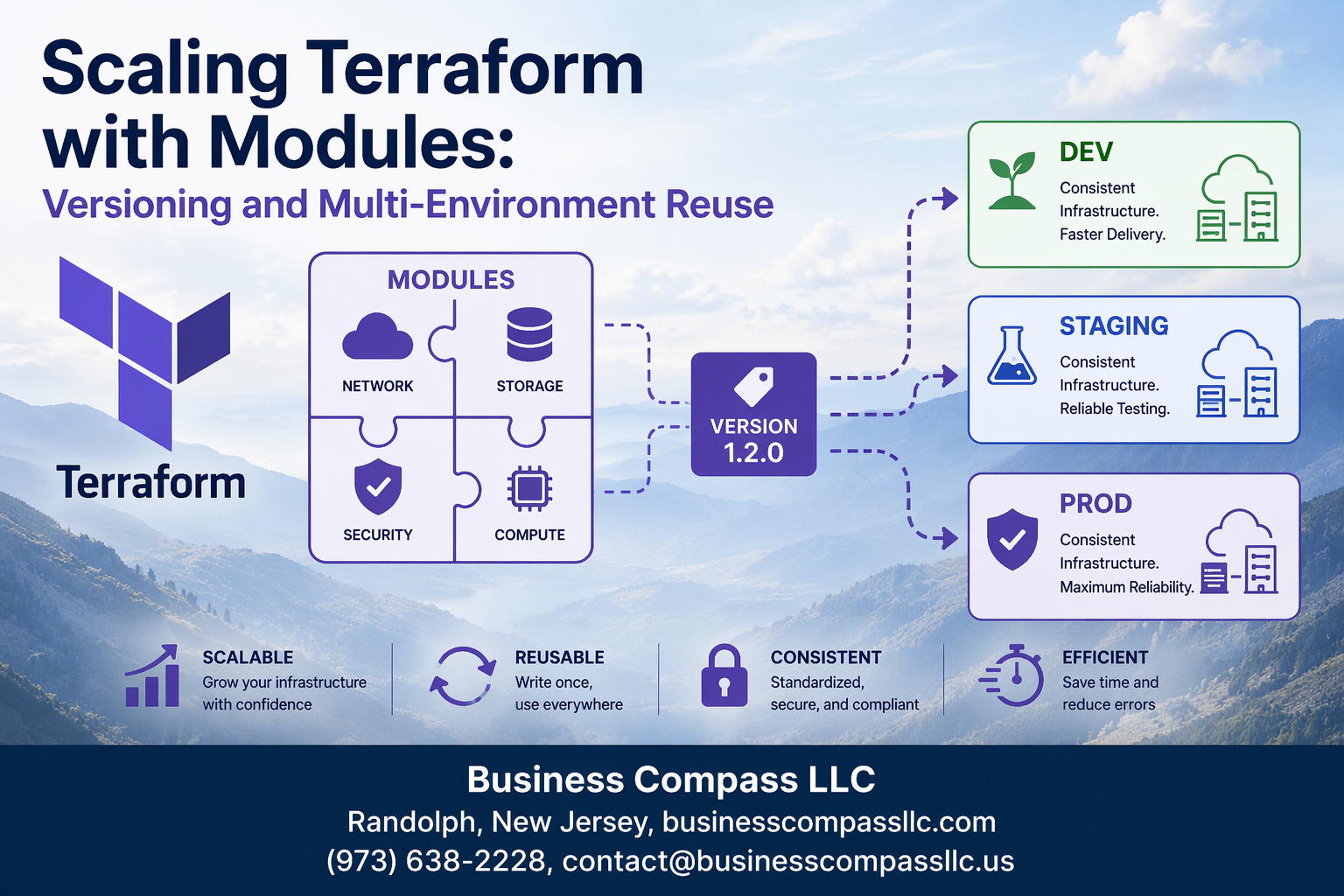
Managing infrastructure across multiple environments gets messy fast without the right approach. Terraform modules solve this problem by letting you package infrastructure components into reusable, versioned building blocks that work consistently across development, staging, and production environments.
This guide is for DevOps engineers, platform teams, and infrastructure developers who want to scale their Terraform infrastructure beyond basic configurations. You’ll learn how to structure reusable Terraform modules that grow with your organization while maintaining consistency and reliability.
We’ll walk through implementing effective module versioning strategies that prevent breaking changes from disrupting your deployments. You’ll also discover how to design modules for multi-environment deployment, ensuring your infrastructure code works seamlessly whether you’re spinning up a quick development environment or deploying to production. Finally, we’ll cover establishing module registry and distribution systems that make sharing and managing Terraform modules across teams simple and secure.
Understanding Terraform Module Fundamentals for Scalable Infrastructure

Define reusable infrastructure components with consistent patterns
Building Terraform modules transforms scattered configuration files into standardized building blocks. Each module encapsulates specific infrastructure patterns—whether it’s a VPC setup, application load balancer, or database cluster—with well-defined inputs and outputs. This approach creates reusable Terraform modules that follow consistent naming conventions, security policies, and architectural decisions across your organization.
Eliminate code duplication across multiple projects
Modules prevent teams from writing the same infrastructure code repeatedly. Instead of copying and pasting Terraform configurations between projects, developers can reference proven modules that handle complex resource relationships. This Infrastructure as Code modules strategy reduces errors, speeds up deployment times, and ensures that battle-tested configurations power new environments.
Establish standardized resource configurations
Terraform module composition enforces organizational standards automatically. Security groups follow company policies, monitoring configurations remain consistent, and resource tagging happens uniformly. Teams can’t accidentally deploy non-compliant infrastructure because the module itself embeds these requirements, making compliance a byproduct of normal development workflows.
Create maintainable infrastructure blueprints
Well-designed modules become living documentation of your infrastructure patterns. They capture architectural decisions, resource dependencies, and operational knowledge in executable code. When infrastructure requirements change, updating a single module propagates improvements across all consuming projects, making scaling Terraform infrastructure manageable even as your environment grows exponentially.
Implementing Effective Module Versioning Strategies
Adopt semantic versioning for predictable updates
Terraform module versioning becomes manageable when you follow semantic versioning (SemVer) patterns like v1.2.3, where major versions indicate breaking changes, minor versions add features, and patches fix bugs. This approach helps teams predict how updates will affect their infrastructure deployments and plan upgrades accordingly.
Maintain backward compatibility across module versions
Smart module design keeps existing functionality intact while adding new features through optional variables with sensible defaults. When you need to change behavior, introduce new parameters instead of modifying existing ones, allowing teams to migrate gradually without breaking their current Infrastructure as Code setups.
Document breaking changes and migration paths
Clear documentation transforms potentially disruptive updates into smooth transitions by providing step-by-step migration guides and highlighting all breaking changes. Include examples showing before-and-after configurations, making it easy for teams to understand exactly what needs updating when they move between Terraform module versions.
Designing Modules for Multi-Environment Deployment

Build environment-agnostic module configurations
Creating environment-agnostic Terraform modules requires careful abstraction of environment-specific details through input variables. Design modules that accept environment context through parameters like environment, region, and project_name rather than hardcoding values. This approach enables seamless reusability across development, staging, and production environments while maintaining Infrastructure as Code consistency.
Use conditional logic within modules to handle environment-specific behaviors without compromising the core module structure. Implement data sources and local values to dynamically determine resource configurations based on the target environment, ensuring your reusable Terraform modules adapt intelligently to different deployment contexts.
Implement variable-driven resource customization
Variable-driven customization forms the backbone of scalable Terraform infrastructure by replacing hardcoded values with configurable parameters. Define comprehensive variable schemas that cover resource specifications, feature toggles, and environment-specific settings. Structure variables with sensible defaults while allowing override capabilities for specialized requirements across different environments.
Leverage variable validation rules and type constraints to ensure consistent inputs while maintaining flexibility. This strategy enables Terraform multi-environment deployment scenarios where the same module can provision appropriately sized resources for development environments versus production workloads.
Handle environment-specific naming conventions
Environment-specific naming conventions prevent resource conflicts and improve infrastructure organization across multiple deployment contexts. Implement naming patterns that incorporate environment identifiers, project codes, and resource types through consistent variable interpolation. Design naming schemas that scale naturally from single environments to complex multi-region, multi-environment scenarios.
Create naming modules or local values that generate standardized resource names based on input parameters. This approach ensures naming consistency while accommodating organizational requirements and cloud provider naming constraints across different environments and regions.
Manage resource sizing differences across environments
Resource sizing strategies must accommodate varying performance and cost requirements across development, staging, and production environments. Design modules with tiered sizing configurations using maps or objects that define appropriate resource specifications for each environment type. This enables cost optimization in lower environments while ensuring production readiness.
Implement dynamic sizing logic that scales resources based on environment classification and workload requirements. Use variable-driven approaches to adjust instance types, storage configurations, and networking capacity, ensuring your Terraform module composition supports both development efficiency and production performance needs.
Establishing Module Registry and Distribution Systems

Set up private module registries for team collaboration
Private Terraform module registries create centralized hubs where teams can securely store and share Infrastructure as Code modules across projects. Organizations can deploy self-hosted registries using Terraform Cloud, GitLab’s package registry, or custom solutions that integrate with existing CI/CD pipelines. These registries enable version control, access management, and seamless module distribution while maintaining organizational security standards.
Implement automated module publishing workflows
Automated publishing workflows streamline the process of releasing new Terraform module versions through CI/CD pipelines. When developers push module updates to version control, automated systems can validate syntax, run tests, and publish approved modules to registries with proper semantic versioning. This approach reduces manual errors and ensures consistent module quality across all published versions.
Create module discovery and documentation systems
Documentation systems make Terraform modules discoverable and usable by providing searchable catalogs with usage examples, input variables, and output descriptions. Teams can implement automated documentation generation tools that extract metadata from module code and create comprehensive guides. These systems often include tagging mechanisms, dependency visualizations, and integration examples that help developers quickly identify suitable modules for their infrastructure needs.
Control access permissions and security policies
Access control mechanisms protect sensitive infrastructure modules while enabling appropriate team collaboration through role-based permissions and authentication systems. Organizations can implement policies that restrict module access based on environment types, team membership, or security clearance levels. Security scanning tools can automatically validate modules for compliance violations, credential exposure, and configuration vulnerabilities before publication to registries.
Managing Dependencies and Module Composition

Structure complex infrastructure through module relationships
Building sophisticated infrastructure requires careful orchestration of module relationships. Think of modules as building blocks that connect through well-defined interfaces – your network module provides VPC outputs that your compute module consumes as inputs. This creates a dependency graph where changes flow predictably through your infrastructure stack, enabling you to manage complex systems without losing control.
Handle cross-module data sharing with outputs and data sources
Smart data sharing between Terraform modules relies on strategic use of outputs and data sources. Export essential information like subnet IDs, security group references, and resource ARNs through module outputs, then import this data in dependent modules using data sources or direct variable passing. This approach maintains loose coupling while ensuring modules can access the information they need to function correctly across your multi-environment deployment.
Resolve version conflicts in module dependency chains
Version conflicts in Terraform module dependency chains can break your entire infrastructure deployment. Pin module versions using semantic versioning in your module blocks, and establish a dependency matrix that tracks which module versions work together. When conflicts arise, update modules incrementally rather than making wholesale changes, testing each version bump in development environments before promoting to production.
Implement module testing and validation processes
Robust testing ensures your Terraform modules work reliably across different scenarios. Create automated tests using tools like Terratest or kitchen-terraform that validate module functionality, check resource creation, and verify outputs match expectations. Include unit tests for individual modules and integration tests for module composition, running these checks in CI/CD pipelines before merging changes to your module registry.
Optimize module load times and resource planning
Module performance directly impacts deployment speed and resource efficiency. Reduce load times by minimizing provider configuration overhead, using data sources judiciously, and avoiding unnecessary resource dependencies. Structure your modules to support parallel execution where possible, and implement resource planning that considers both current needs and future scaling requirements for your Infrastructure as Code modules.

Building scalable infrastructure with Terraform modules really comes down to smart planning and consistent practices. When you set up proper versioning, design modules that work across different environments, and create a solid distribution system, you’re essentially building a foundation that grows with your team and projects. The key is treating your modules like any other piece of software – they need clear documentation, thoughtful dependency management, and a reliable way to share them across your organization.
Start small with a few well-designed modules and gradually expand your library as you learn what works best for your specific use cases. Focus on creating modules that solve real problems your team faces regularly, and don’t forget to establish clear naming conventions and versioning practices from day one. Your future self (and your teammates) will thank you when you can deploy complex infrastructure changes with confidence, knowing that your modular approach keeps everything organized and maintainable.