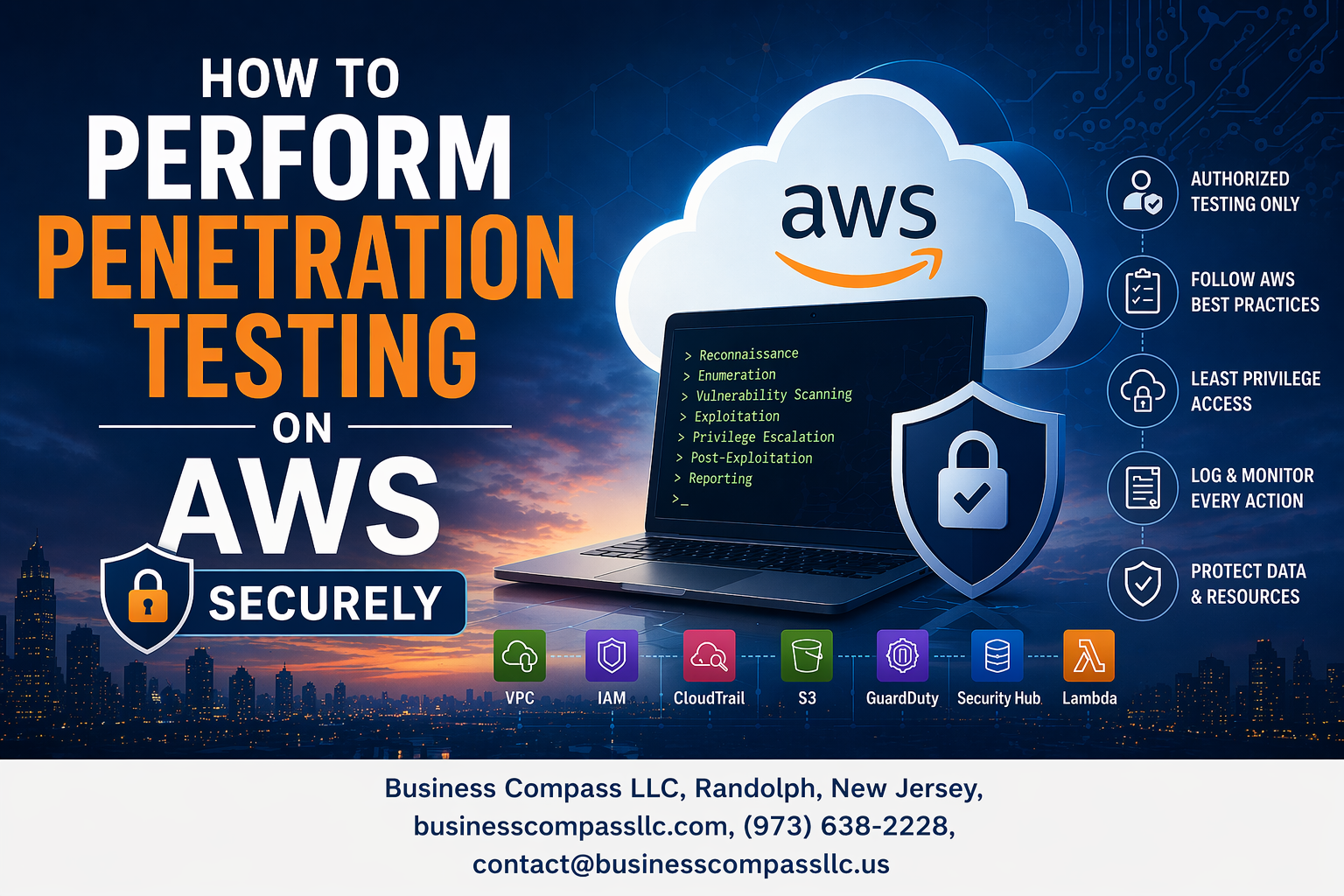
AWS penetration testing requires careful planning and specialized knowledge to identify vulnerabilities without disrupting your cloud infrastructure. This comprehensive AWS pentesting guide is designed for security professionals, cloud engineers, and IT teams who need to conduct thorough security assessments while following Amazon’s strict testing policies.
AWS infrastructure security testing presents unique challenges that traditional on-premises pentesting doesn’t cover. You’ll need to understand AWS-specific attack vectors, comply with Amazon’s customer agreement requirements, and maintain operational security throughout your testing process.
We’ll walk you through the essential pre-testing preparation and environment setup you need before touching any AWS resources. You’ll learn core AWS infrastructure penetration testing techniques that target the most common cloud vulnerabilities. We’ll also cover advanced cloud-specific attack simulation methods that help you test complex multi-service architectures and identify privilege escalation paths that attackers commonly exploit in cloud environments.
Understanding AWS Penetration Testing Requirements and Legal Framework

Navigate AWS Customer Agreement and Acceptable Use Policy
AWS penetration testing requires careful navigation of legal frameworks before launching any security assessment. Review the AWS Customer Agreement thoroughly, as it outlines your responsibilities and limitations when conducting penetration testing AWS infrastructure. The Acceptable Use Policy specifically prohibits certain activities that could impact other customers or violate service terms.
Pay close attention to prohibited activities like network scanning beyond your allocated resources, attempting to access other customers’ data, or overwhelming AWS services with excessive traffic. Document these restrictions in your testing plan to avoid accidental violations that could result in service suspension or legal action.
Identify Pre-Authorized Services vs Services Requiring AWS Approval
AWS divides services into two categories for cloud security testing purposes. Pre-authorized services include EC2 instances, RDS, CloudFront, Lambda, API Gateway, Lightsail, and Elastic Beanstalk. These services allow penetration testing without prior AWS notification, giving you flexibility for most AWS security assessment scenarios.
Services requiring AWS approval include DNS zone walking attempts against Route 53, DDoS simulations, flooding attacks, and testing that might affect shared infrastructure. Submit requests through the AWS Vulnerability and Penetration Testing form at least two weeks before testing. Include detailed scope, methodology, and timeline information for approval.
Document Compliance Requirements for Your Industry
Industry-specific compliance frameworks significantly impact your AWS pentesting guide approach. Healthcare organizations must consider HIPAA requirements, while financial institutions need SOX and PCI DSS compliance. Government contractors face FedRAMP and FISMA obligations that influence testing scope and documentation requirements.
Create a compliance matrix mapping your industry standards to AWS penetration testing activities. Include data handling requirements, reporting formats, and retention policies. Document how your testing methodology aligns with frameworks like SOC 2, ISO 27001, or GDPR to satisfy auditors and regulatory bodies.
Establish Clear Scope and Boundaries for Testing
Define precise boundaries for your penetration testing best practices AWS implementation to prevent scope creep and legal issues. Identify specific AWS accounts, regions, and services included in testing while explicitly documenting excluded resources. Create network diagrams showing test targets and off-limits systems to guide your team.
Establish testing windows, communication protocols, and escalation procedures before beginning cloud penetration testing methodology activities. Include emergency contact information for both your team and AWS support. Document rollback procedures and system recovery plans to minimize business impact during aggressive testing phases.
Essential Pre-Testing Preparation and Environment Setup

Create Isolated Testing Environment Within Your AWS Account
Setting up a dedicated testing environment prevents accidental damage to production systems during AWS penetration testing activities. Create separate VPCs with isolated subnets, ensuring complete network segregation from critical infrastructure. Deploy test instances that mirror your production architecture while maintaining strict boundaries through security groups and NACLs.
Configure your testing environment with limited external connectivity and implement proper tagging strategies for easy identification. This isolated approach allows comprehensive AWS security assessment without risking operational systems, enabling thorough penetration testing AWS infrastructure while maintaining business continuity throughout the security evaluation process.
Configure Proper IAM Roles and Permissions for Security Testing
Establish specialized IAM roles with carefully scoped permissions that balance testing needs with security constraints. Create policies that grant necessary access for cloud security testing while preventing privilege escalation beyond the testing environment. Implement temporary credentials with time-based restrictions and multi-factor authentication requirements.
Design role hierarchies that separate testing personnel from production access, ensuring penetration testing best practices AWS compliance. Configure cross-account roles when testing multiple AWS accounts, maintaining audit trails for all security testing activities while preventing unauthorized access to sensitive resources during your AWS pentesting guide implementation.
Set Up Comprehensive Logging and Monitoring Systems
Enable CloudTrail across all testing regions to capture detailed API activity logs during secure cloud penetration testing sessions. Configure VPC Flow Logs, GuardDuty, and Security Hub to monitor network traffic patterns and detect unusual activities. Set up centralized logging using CloudWatch and S3 buckets with proper retention policies.
Implement real-time alerting for suspicious activities that could indicate testing boundaries have been exceeded. Configure monitoring dashboards that track resource usage, network connections, and authentication attempts during AWS compliance penetration testing. This comprehensive logging framework ensures complete visibility into all testing activities while supporting post-assessment analysis and compliance reporting requirements.
Core AWS Infrastructure Penetration Testing Techniques

Assess EC2 Instance Security and Network Configuration
Start your AWS penetration testing by examining EC2 instances for common security gaps. Check for unpatched operating systems, weak SSH key management, and overly permissive security group rules that expose unnecessary ports. Test for privilege escalation vulnerabilities and verify that instances aren’t running with excessive IAM permissions that could lead to lateral movement across your cloud environment.
Network configuration testing involves validating subnet isolation and examining how instances communicate across availability zones. Look for misconfigurations in elastic load balancers, auto-scaling groups, and network ACLs that might create unintended access paths. Pay special attention to instances with public IP addresses and ensure they have proper monitoring and logging enabled to detect suspicious activities.
Evaluate S3 Bucket Permissions and Data Exposure Risks
S3 bucket security assessment requires careful examination of access control lists, bucket policies, and public access settings. Many data breaches stem from misconfigured S3 buckets that accidentally expose sensitive information to the internet. Test for read and write permissions, check versioning configurations, and verify that encryption is properly implemented both in transit and at rest.
Focus on identifying buckets with overly broad permissions or those lacking proper authentication mechanisms. Review cross-account access policies and ensure that temporary credentials aren’t being misused. Test the effectiveness of S3 access logging and CloudTrail integration to ensure you can track who accessed what data and when.
Test VPC Security Groups and Network Access Controls
VPC security group testing forms the backbone of AWS infrastructure security assessment. Examine inbound and outbound rules for each security group, looking for overly permissive configurations like 0.0.0.0/0 source addresses on critical ports. Test how security groups interact with each other and verify that the principle of least privilege is properly enforced across your network architecture.
Network access control testing should include examining route tables, internet gateways, and NAT configurations. Check for proper network segmentation between different environments and ensure that private subnets truly remain isolated from public internet access. Validate that VPC flow logs capture sufficient detail for security monitoring and incident response.
Analyze RDS Database Security and Access Management
Database security testing begins with examining authentication mechanisms, encryption settings, and backup configurations. Test for default credentials, weak passwords, and verify that database instances aren’t publicly accessible unless absolutely necessary. Check that SSL/TLS connections are enforced and that encryption at rest is properly configured with appropriate key management.
Access management testing should focus on database user permissions, role-based access controls, and integration with AWS IAM. Examine database parameter groups for security-related settings and test the effectiveness of automated backups and point-in-time recovery options. Verify that database activity logging captures sufficient detail for compliance and security monitoring requirements.
Review Lambda Function Security and Serverless Vulnerabilities
Lambda function security assessment requires examining function permissions, environment variables, and dependencies for potential vulnerabilities. Test for overly broad IAM roles attached to functions and check for hardcoded secrets or API keys within function code. Examine how functions handle input validation and whether they’re susceptible to injection attacks or other common application vulnerabilities.
Serverless security testing extends to examining API Gateway configurations, event source mappings, and cross-service permissions. Check for proper error handling that doesn’t leak sensitive information and verify that functions have appropriate timeout and memory limits. Test the security of deployment packages and ensure that third-party libraries are regularly updated to address known vulnerabilities.
Advanced Cloud-Specific Attack Simulation Methods

Perform IAM Privilege Escalation Testing
Testing IAM privilege escalation requires systematically examining role permissions and trust relationships to identify potential attack paths. Start by mapping out existing roles, policies, and cross-account trusts using tools like ScoutSuite or Prowler. Focus on overprivileged service accounts, wildcard permissions, and AssumeRole chains that could allow lateral movement.
Create test scenarios that simulate attackers exploiting misconfigured IAM policies to gain elevated access. Test common escalation vectors like excessive S3 permissions leading to credential exposure, or Lambda functions with overly broad execution roles that could access sensitive resources across your AWS infrastructure.
Execute Cross-Service Resource Access Validation
Cross-service access validation examines how different AWS services interact and whether proper isolation exists between environments. Test VPC peering configurations, security group rules, and network ACLs to identify unauthorized communication paths. Pay special attention to services like ECS, EKS, and Lambda that might access resources across multiple availability zones.
Validate that service-to-service authentication properly restricts access based on least privilege principles. Test scenarios where compromised EC2 instances attempt to access RDS databases, S3 buckets, or other services without proper authorization, ensuring your security controls effectively prevent unauthorized cross-service data access.
Test API Gateway Security and Authentication Mechanisms
API Gateway security testing focuses on authentication bypass, authorization flaws, and rate limiting effectiveness. Test various authentication methods including API keys, JWT tokens, and AWS IAM authentication to identify weaknesses. Examine custom authorizers for logic flaws that could allow unauthorized access to backend services.
Validate rate limiting configurations and DDoS protection mechanisms by simulating high-volume requests and testing throttling behaviors. Check for common API vulnerabilities like injection attacks, broken object level authorization, and improper error handling that could expose sensitive information about your cloud infrastructure.
Simulate Data Exfiltration Scenarios
Data exfiltration simulation tests your ability to detect and prevent unauthorized data movement from AWS environments. Create realistic scenarios involving S3 bucket enumeration, database dumps, and large file transfers that mimic actual attacker behavior. Test both obvious exfiltration attempts and subtle, low-and-slow data theft patterns.
Implement monitoring for unusual data access patterns, unexpected API calls, and abnormal network traffic that could indicate ongoing exfiltration attempts. Validate that your security monitoring tools can effectively detect when sensitive data is being accessed or transferred outside normal business processes.
Maintaining Security and Compliance During Testing

Implement Real-Time Monitoring to Prevent Service Disruption
Setting up comprehensive monitoring during AWS penetration testing protects your production environment from unexpected impacts. CloudWatch metrics, AWS X-Ray, and third-party monitoring tools help track resource usage, performance degradation, and unusual activity patterns. Configure alerts for CPU spikes, memory exhaustion, network anomalies, and failed authentication attempts to catch issues before they escalate. This proactive approach keeps your AWS infrastructure stable while allowing thorough security assessment.
Real-time dashboards give you instant visibility into system health during penetration testing activities. Monitor database connections, API call rates, and service response times to detect when testing pushes systems beyond normal operating parameters. Automated circuit breakers can pause testing when critical thresholds are reached, preventing service outages that could impact business operations or customer experience.
Use Non-Production Data to Avoid Compliance Violations
Working with sanitized datasets eliminates the risk of exposing sensitive information during AWS security testing. Create realistic test data that mirrors production structures without containing actual customer records, payment information, or personally identifiable data. Data masking and synthetic data generation tools help build comprehensive test environments that support thorough penetration testing while meeting regulatory requirements like GDPR, HIPAA, and PCI DSS.
Separate AWS accounts for penetration testing create clear boundaries between production and test environments. This isolation prevents accidental data exposure and simplifies compliance auditing. Copy database schemas and application structures to dedicated testing accounts, then populate them with anonymized information that maintains the complexity needed for effective security assessment without regulatory risks.
Document All Testing Activities for Audit Trails
Detailed logging of every penetration testing action creates the documentation needed for compliance frameworks and security audits. Record test scenarios, tools used, vulnerabilities discovered, and remediation steps taken. Time-stamped logs show exactly what happened during each testing phase, making it easy to correlate security events with specific testing activities. This documentation proves due diligence to auditors and regulatory bodies.
Structured reporting templates capture both technical findings and business impact assessments from AWS penetration testing. Include screenshots, command outputs, and vulnerability ratings alongside explanations of potential risks and recommended fixes. Store all documentation in secure, version-controlled repositories that maintain chain of custody and provide easy access for future reference or follow-up assessments.
Post-Testing Analysis and Remediation Planning

Generate Comprehensive Vulnerability Reports with Risk Ratings
Creating detailed vulnerability reports forms the cornerstone of effective AWS penetration testing outcomes. Your reports should categorize findings by severity levels—critical, high, medium, and low—while incorporating AWS-specific risk factors like IAM misconfigurations, S3 bucket exposures, and security group vulnerabilities. Each vulnerability entry must include technical descriptions, proof-of-concept evidence, and potential business impact to help stakeholders understand the real-world implications.
Prioritize Findings Based on Business Impact and Exploitability
Smart prioritization goes beyond simple CVSS scores when dealing with AWS infrastructure security testing. Focus on vulnerabilities that could lead to data breaches, service disruptions, or compliance violations specific to your cloud environment. Consider factors like asset criticality, data sensitivity, and attack complexity to build a realistic threat landscape that guides remediation efforts effectively.
Develop Actionable Remediation Roadmap with Timelines
Transform your AWS security assessment findings into a practical action plan with clear ownership and realistic deadlines. Break down complex fixes into manageable phases, starting with quick wins like tightening security groups or enabling CloudTrail logging. Your roadmap should account for business operations, maintenance windows, and resource availability while maintaining the security improvements’ effectiveness.
Verify Fixes Through Controlled Re-Testing
Validation testing ensures your remediation efforts actually close security gaps without creating new ones. Design focused re-tests that target specific vulnerabilities while monitoring for unintended consequences in your AWS environment. Document the verification process thoroughly, including before-and-after configurations, to demonstrate compliance improvements and maintain a clear audit trail for future penetration testing cycles.

AWS penetration testing requires careful planning and execution to ensure you get meaningful results without compromising your cloud environment. The key lies in understanding AWS’s customer responsibility model, setting up proper test environments, and following approved testing methodologies that respect both legal boundaries and security best practices. From obtaining necessary permissions to implementing advanced attack simulations, each step builds toward a comprehensive security assessment that reveals genuine vulnerabilities.
The real value comes from what you do after the testing ends. Document everything thoroughly, prioritize findings based on actual risk to your business, and create actionable remediation plans that your team can implement. Remember to schedule regular testing cycles since cloud environments evolve rapidly, and new threats emerge constantly. Start with a limited scope for your first penetration test, learn from the process, and gradually expand your testing program as your team becomes more comfortable with cloud security assessment techniques.