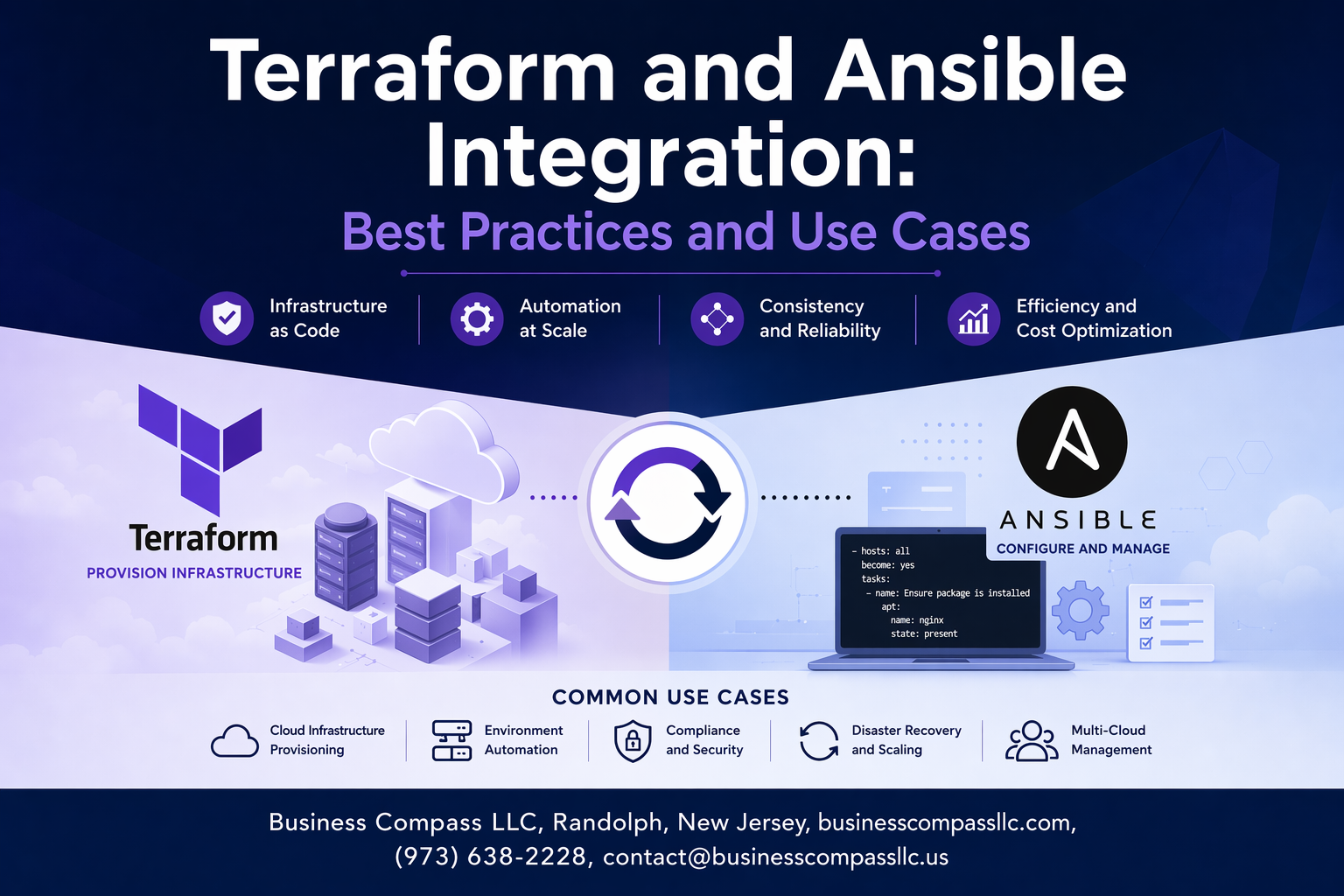
Managing cloud infrastructure and application configuration can feel overwhelming when you’re juggling multiple tools. Terraform ansible integration offers a powerful solution that combines infrastructure provisioning with configuration management, creating streamlined devops automation workflows that scale with your business needs.
This guide targets DevOps engineers, infrastructure teams, and cloud architects who want to master terraform and ansible best practices for their organization’s automation strategy. You’ll discover practical approaches that eliminate the guesswork from infrastructure as code ansible implementations.
We’ll explore proven integration patterns that show exactly how these infrastructure automation tools work together in production environments. You’ll also see real-world terraform ansible use cases from companies that have successfully implemented these solutions, plus actionable strategies to optimize performance and troubleshoot common integration challenges that teams face during deployment.
Understanding the Synergy Between Terraform and Ansible
Leveraging Infrastructure as Code with Configuration Management
Terraform and Ansible integration creates a powerful synergy where infrastructure provisioning meets application configuration. Terraform excels at creating cloud resources, networks, and compute instances through declarative infrastructure as code, while Ansible handles the detailed configuration management tasks that transform bare infrastructure into functional systems.
This combination eliminates the traditional gap between infrastructure deployment and application readiness. Terraform ansible provisioning workflows can automatically trigger Ansible playbooks once resources are created, ensuring seamless transitions from infrastructure creation to software installation, security hardening, and service configuration across your entire environment.
Maximizing Deployment Efficiency Through Tool Combination
DevOps automation workflows benefit tremendously when Terraform handles resource lifecycle management while Ansible manages ongoing configuration drift and updates. This division of responsibilities reduces deployment complexity and allows teams to leverage each tool’s strengths without overlap or conflict.
Terraform ansible configuration management patterns enable rapid scaling scenarios where new infrastructure can be provisioned and configured in minutes rather than hours. Teams can standardize both infrastructure blueprints and configuration templates, creating repeatable deployment processes that maintain consistency across development, staging, and production environments.
Achieving End-to-End Automation Workflows
Infrastructure automation tools working together create comprehensive pipelines that handle everything from initial resource creation to ongoing maintenance and updates. Terraform’s state management combined with Ansible’s idempotent configuration ensures that environments remain consistent and can be easily reproduced or modified as requirements change.
Ansible terraform orchestration enables sophisticated deployment strategies like blue-green deployments, rolling updates, and disaster recovery scenarios. This integrated approach allows teams to implement complex infrastructure patterns while maintaining full visibility and control over both the underlying resources and the applications running on them.
Essential Prerequisites for Successful Integration

Setting Up Terraform Backend Configuration
Remote state management forms the backbone of successful terraform ansible integration. Configure your backend using S3 or Azure Blob Storage with state locking through DynamoDB or Consul to prevent concurrent modifications. This setup allows Ansible to reliably access Terraform outputs and infrastructure metadata.
Enable versioning on your state backend and implement proper access controls. Your backend configuration should include encryption at rest and transit, making it accessible to both Terraform and Ansible workflows while maintaining security boundaries across your devops automation workflows.
Configuring Ansible Inventory Management
Dynamic inventory configuration bridges the gap between Terraform-provisioned infrastructure and Ansible’s configuration management capabilities. Set up inventory plugins that automatically discover resources from your cloud providers or use Terraform’s local-exec provisioner to generate inventory files during infrastructure deployment.
Configure inventory sources to pull instance metadata, tags, and network information directly from your cloud APIs. This approach eliminates manual inventory maintenance and ensures your Ansible playbooks always target the correct infrastructure components created by Terraform.
Establishing Secure Authentication Mechanisms
Implement service principal authentication for cloud providers using environment variables or dedicated credential files accessible to both tools. Configure Terraform to use the same authentication method as Ansible, creating a unified identity management approach across your infrastructure automation tools.
Set up SSH key management for Ansible connectivity to Terraform-provisioned instances. Store private keys securely using cloud key vaults or encrypted storage, and configure Terraform to inject public keys during instance creation for seamless Ansible access.
Installing Required Plugins and Providers
Install essential Terraform providers for your target cloud platforms and the local, null, and external providers for Ansible integration points. These providers enable terraform ansible provisioning patterns and data exchange between the two tools during deployment workflows.
Add Ansible’s cloud collection modules and dynamic inventory plugins for your infrastructure platform. Configure the Terraform provider for Ansible if using advanced integration patterns, ensuring both tools can communicate effectively throughout your deployment pipeline.
Proven Integration Patterns and Methodologies

Using Terraform to Provision Infrastructure for Ansible
Terraform serves as the perfect foundation layer for ansible terraform orchestration, creating consistent infrastructure environments where Ansible can execute configuration management tasks. When Terraform provisions cloud resources like EC2 instances, VPCs, and security groups, it automatically generates outputs containing IP addresses, hostnames, and connection details that Ansible requires. This terraform ansible integration approach eliminates manual inventory management and reduces deployment errors significantly.
The most effective pattern involves Terraform creating infrastructure components with standardized tags and metadata that Ansible can consume directly. By structuring Terraform modules to output essential connection parameters, teams establish a seamless handoff between infrastructure provisioning and configuration management phases of their devops automation workflows.
Implementing Dynamic Inventory Generation
Dynamic inventory generation transforms static Ansible inventory files into intelligent, real-time infrastructure discovery mechanisms. Terraform can automatically create Ansible inventory files using local-exec provisioners or template resources, pulling fresh infrastructure data from cloud providers’ APIs. This terraform ansible deployment pattern ensures inventory accuracy and eliminates configuration drift between actual infrastructure and Ansible’s understanding of the environment.
Advanced implementations leverage Terraform’s external data sources to query cloud provider APIs, generating JSON or INI formatted inventory files that include grouping logic, host variables, and connection parameters. This infrastructure automation approach scales effortlessly as environments grow and change.
Executing Ansible Playbooks Through Terraform Provisioners
Local-exec and remote-exec provisioners enable direct Ansible playbook execution within Terraform workflows, creating unified infrastructure as code ansible pipelines. The local-exec provisioner runs Ansible commands from the Terraform execution environment, while remote-exec connects directly to provisioned instances for immediate configuration tasks. This terraform ansible configuration management pattern works particularly well for initial system setup and application deployment scenarios.
Smart provisioner implementations include retry logic, environment variable passing, and conditional execution based on resource states. Teams can trigger specific playbooks based on infrastructure changes, ensuring configuration consistency across dynamic environments while maintaining the benefits of both tools.
Creating Modular Workflows with External Data Sources
External data sources bridge the gap between Terraform’s infrastructure provisioning and Ansible’s configuration management by enabling real-time data exchange between tools. Terraform can query Ansible facts, inventory databases, or configuration management systems to make infrastructure decisions based on current system states. This bidirectional communication creates sophisticated terraform ansible best practices that adapt to changing requirements automatically.
Modular workflow designs separate concerns while maintaining integration points through well-defined data contracts. Teams build reusable Terraform modules that consume Ansible-generated configuration data, while Ansible roles adapt to Terraform-provisioned infrastructure characteristics, creating flexible devops automation workflows that scale across multiple environments and use cases.
Real-World Use Cases Delivering Maximum Value

Multi-Cloud Infrastructure Deployment and Configuration
Terraform and Ansible integration shines when deploying infrastructure across AWS, Azure, and Google Cloud simultaneously. Terraform provisions the foundational resources like VPCs, subnets, and compute instances across multiple cloud providers, while Ansible handles the detailed configuration management. This terraform ansible deployment pattern ensures consistent application environments regardless of the underlying cloud platform, reducing vendor lock-in and improving disaster recovery capabilities.
DevOps automation workflows become streamlined when teams leverage Terraform’s cloud-agnostic provisioning capabilities alongside Ansible’s powerful configuration management. Organizations can maintain identical security policies, monitoring setups, and application configurations across different cloud environments. This terraform ansible orchestration approach significantly reduces deployment complexity and operational overhead while maintaining compliance standards.
Container Orchestration Platform Setup
Setting up Kubernetes clusters demonstrates the power of terraform ansible integration in complex orchestration scenarios. Terraform creates the underlying infrastructure including master nodes, worker nodes, load balancers, and networking components across your preferred cloud provider. Ansible then configures the Kubernetes control plane, installs necessary add-ons like ingress controllers, and sets up monitoring solutions like Prometheus and Grafana.
Infrastructure automation tools work together seamlessly to handle post-provisioning tasks that Terraform cannot manage effectively. Ansible playbooks configure kubectl access, deploy essential operators, and establish cluster-wide policies. This terraform ansible configuration management approach ensures your Kubernetes environment is production-ready with proper security contexts, resource quotas, and network policies configured automatically.
Database Cluster Provisioning and Initial Configuration
Database cluster deployment showcases advanced terraform ansible use cases where infrastructure provisioning meets complex application configuration. Terraform provisions database instances, storage volumes, security groups, and networking components for high-availability PostgreSQL or MySQL clusters. The integration ensures proper subnet placement, backup storage configuration, and security group rules are established before any database software touches the servers.
Ansible handles the intricate database initialization tasks that require application-level knowledge. Ansible terraform orchestration manages database engine installation, cluster formation, replication setup, and initial schema deployment. This infrastructure as code ansible approach includes user creation, permission assignment, and backup job configuration, delivering fully functional database clusters ready for production workloads without manual intervention.
Performance Optimization and Security Best Practices

Implementing State Management for Large-Scale Deployments
Managing Terraform state files becomes critical when orchestrating infrastructure automation tools across multiple environments. Remote state backends like AWS S3 or Terraform Cloud prevent conflicts while enabling team collaboration. State locking mechanisms ensure terraform ansible integration workflows don’t corrupt infrastructure configurations during concurrent operations.
Securing Sensitive Data with Vault Integration
HashiCorp Vault seamlessly integrates with both Terraform and Ansible to protect credentials and secrets. Configure Vault providers in Terraform modules while using Ansible’s vault lookup plugins for runtime secret retrieval. This approach ensures terraform and ansible best practices maintain zero-trust security across your devops automation workflows.
Optimizing Execution Time Through Parallel Processing
Terraform’s built-in parallelism combined with Ansible’s async execution significantly reduces deployment time. Configure Terraform’s -parallelism flag appropriately while leveraging Ansible’s async and poll parameters for long-running tasks. These terraform ansible deployment patterns maximize resource efficiency during infrastructure provisioning.
Establishing Proper Error Handling and Rollback Procedures
Implement comprehensive error handling using Terraform’s lifecycle rules and Ansible’s error handling blocks. Create automated rollback procedures that preserve infrastructure state consistency when terraform ansible configuration management operations fail. Monitor execution logs and establish clear escalation paths for critical deployment failures.
Common Integration Challenges and Proven Solutions

Resolving State Synchronization Issues
State drift happens when Terraform’s infrastructure state conflicts with actual resource configurations managed by Ansible. The most effective solution involves implementing state refresh strategies before each Terraform run and using remote state backends with locking mechanisms. Teams should establish clear ownership boundaries—Terraform handles infrastructure provisioning while Ansible manages configuration drift detection through regular playbook runs.
Managing Dependencies Between Infrastructure and Configuration
Dependency management requires careful orchestration between terraform ansible integration workflows. Use Terraform outputs to pass critical infrastructure details like IP addresses and security group IDs to Ansible inventories. Implement conditional checks in Ansible playbooks to verify infrastructure readiness before configuration deployment. The terraform-ansible-provisioner pattern works best for seamless handoffs between infrastructure creation and application configuration.
Troubleshooting Network Connectivity Problems
Network connectivity failures often stem from security group misconfigurations or timing issues during infrastructure deployment. Debug connection problems by validating SSH key propagation and ensuring Ansible control nodes can reach target instances through proper routing rules. Use Terraform’s connection provisioners sparingly and prefer Ansible’s wait_for modules to handle network readiness checks before executing configuration tasks.

Terraform and Ansible work incredibly well together when you get the setup right. Terraform handles your infrastructure provisioning while Ansible takes care of configuration management, creating a powerful automation pipeline that can handle everything from cloud resources to application deployment. The key is understanding when to use each tool and how to structure your workflows for maximum efficiency.
Start small with simple integration patterns before moving to more complex scenarios. Keep your security credentials separate, use consistent naming conventions, and always test your automation in non-production environments first. When you hit roadblocks – and you will – remember that most integration challenges have proven solutions. The time you invest in getting this right will pay off with faster deployments, fewer manual errors, and infrastructure that scales with your needs.