Secure Credential Management in Automated Build Systems
Your CI/CD pipeline is only as secure as its weakest credential. For DevOps engineers, security architects, and platform teams managing automated build systems, exposed API keys, hardcoded passwords, and misconfigured secrets create attack vectors that can compromise entire infrastructure networks.
This guide walks through practical approaches to secure credential management that protect your build environments without slowing down development velocity. You’ll discover how to implement robust secret storage solutions that integrate seamlessly with existing workflows, establish role-based access control builds that limit credential exposure, and adopt zero trust CI/CD principles that treat every access request as potentially malicious.
We’ll cover proven strategies for automating credential rotation to reduce manual security overhead, plus monitoring techniques that help you spot unusual credential usage patterns before they become security incidents.
Understanding Credential Vulnerabilities in Build Environments
Identifying Common Security Risks in CI/CD Pipelines
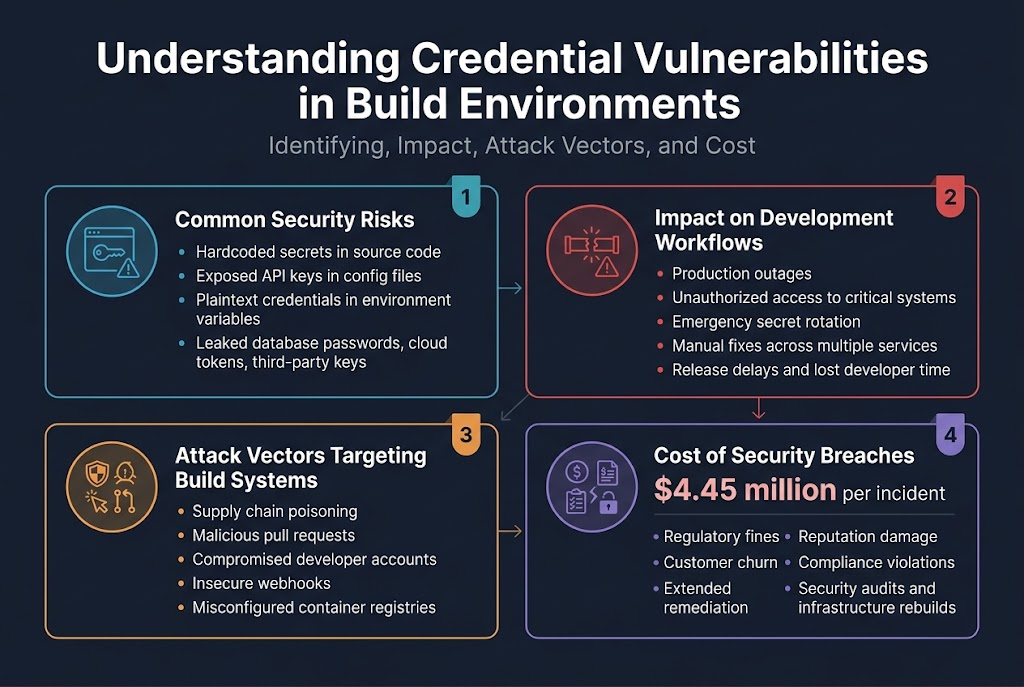
Build system security faces constant threats from hardcoded secrets in source code, exposed API keys in configuration files, and plaintext credentials stored in environment variables. These build environment vulnerabilities create entry points for attackers who scan repositories for leaked database passwords, cloud service tokens, and third-party integration keys. Automated build credentials often get accidentally committed to version control, shared across multiple environments without proper rotation, or stored in unsecured pipeline configurations that lack encryption.
Analyzing Impact of Exposed Secrets on Development Workflows
When secrets leak from CI/CD pipelines, development teams face immediate production outages, unauthorized access to critical systems, and expensive remediation efforts. Exposed credentials force emergency rotation cycles that disrupt release schedules, require manual intervention across multiple services, and create cascading failures in dependent systems. Teams spend valuable development time investigating breach scope, updating affected services, and implementing emergency patches instead of delivering new features.
Recognizing Attack Vectors Targeting Build Systems
Attackers exploit weak secure credential management through supply chain poisoning, malicious pull requests that extract secrets during build processes, and compromised developer accounts with elevated pipeline permissions. Build servers become prime targets because they typically have broad access to production resources, third-party services, and sensitive data stores. Sophisticated attacks inject malicious code into dependency updates, exploit insecure webhook configurations, and leverage misconfigured container registries to steal authentication tokens.
Assessing Cost of Security Breaches in Automated Environments
Security breaches in automated build systems cost organizations an average of $4.45 million per incident, including regulatory fines, customer churn, and extended remediation efforts. Beyond direct financial losses, teams face reputation damage, compliance violations, and lengthy recovery periods that can span months. The hidden costs include developer productivity loss, mandatory security audits, legal fees, and the substantial investment required to rebuild compromised CI/CD infrastructure with proper secret management in DevOps practices.
Implementing Secure Secret Storage Solutions
Leveraging Cloud-Based Key Management Services
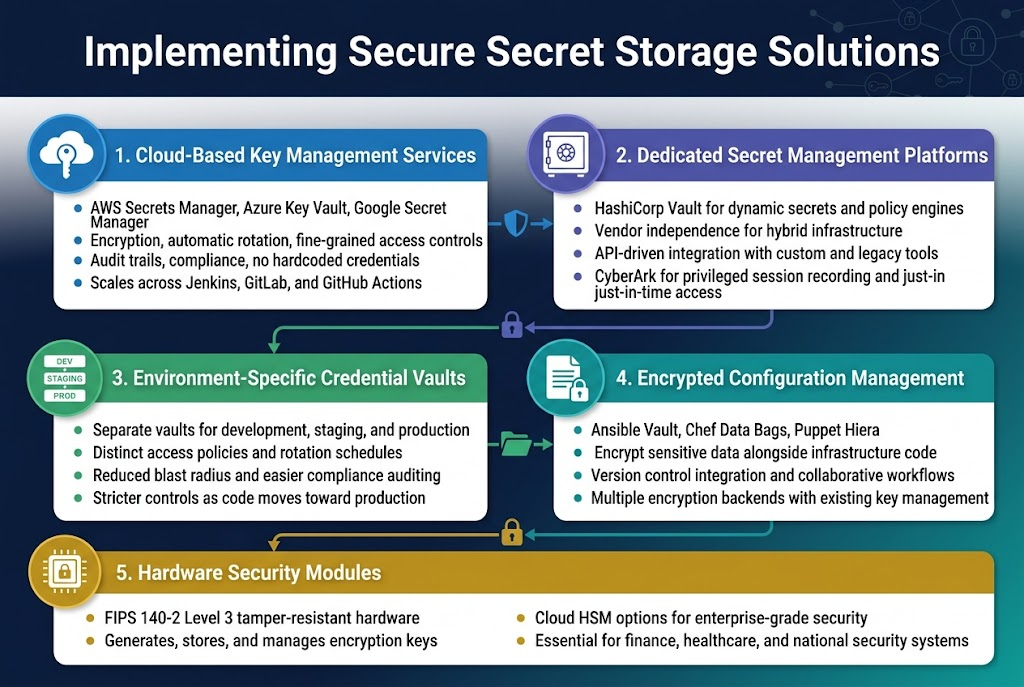
Modern cloud providers offer robust key management services that seamlessly integrate with automated build systems. AWS Secrets Manager, Azure Key Vault, and Google Secret Manager provide enterprise-grade encryption, automatic rotation capabilities, and fine-grained access controls. These services eliminate the need for hardcoded credentials in build scripts while offering built-in audit trails and compliance features.
Cloud-based solutions excel at scaling across distributed build environments and provide native integration with popular CI/CD platforms like Jenkins, GitLab, and GitHub Actions. The managed nature of these services reduces operational overhead while ensuring credentials remain encrypted both at rest and in transit throughout the build process.
Deploying Dedicated Secret Management Platforms
HashiCorp Vault stands as the industry standard for dedicated secret management, offering dynamic secret generation and sophisticated policy engines for build system security. Unlike cloud-native solutions, dedicated platforms provide vendor independence and can operate across hybrid infrastructure environments. Vault’s API-driven architecture enables seamless integration with custom build tools and legacy systems.
CyberArk and other enterprise secret management platforms deliver advanced features like privileged session recording and just-in-time access for critical build environments. These solutions excel in heavily regulated industries where compliance requirements demand granular control over credential access patterns and comprehensive audit capabilities.
Utilizing Environment-Specific Credential Vaults
Segregating credentials by environment prevents accidental cross-contamination between development, staging, and production build processes. Each environment should maintain its own credential vault with distinct access policies and rotation schedules. This approach minimizes blast radius when credential compromise occurs and simplifies compliance auditing across different deployment stages.
Environment-specific vaults enable teams to implement progressive security controls, applying stricter policies as code moves closer to production. Development environments might allow broader access for debugging purposes, while production vaults enforce strict just-in-time access patterns and require multi-factor authentication for credential retrieval.
Establishing Encrypted Configuration Management
Configuration management tools like Ansible Vault, Chef Data Bags, and Puppet Hiera provide built-in encryption capabilities for managing build credentials alongside infrastructure code. These tools encrypt sensitive data using strong ciphers while maintaining version control integration and collaborative workflows. Encrypted configuration management bridges the gap between infrastructure-as-code practices and secure credential storage solutions.
Modern configuration management platforms support multiple encryption backends, allowing teams to integrate with existing key management infrastructure. This approach ensures credentials remain protected even when configuration files are stored in version control systems, enabling secure collaboration without exposing sensitive build environment data.
Integrating Hardware Security Modules for Critical Systems
Hardware Security Modules (HSMs) provide the highest level of security for protecting cryptographic keys used in critical build systems. FIPS 140-2 Level 3 certified HSMs offer tamper-resistant hardware that generates, stores, and manages encryption keys with unparalleled security guarantees. These devices prevent key extraction even under physical attack scenarios.
Cloud HSMs from major providers offer HSM capabilities without requiring dedicated hardware investment, making enterprise-grade security accessible to organizations of all sizes. HSM integration becomes essential for build systems handling sensitive data like financial transactions, healthcare records, or national security applications where regulatory compliance demands hardware-backed security controls.
Establishing Role-Based Access Controls for Build Credentials
Designing Granular Permission Frameworks
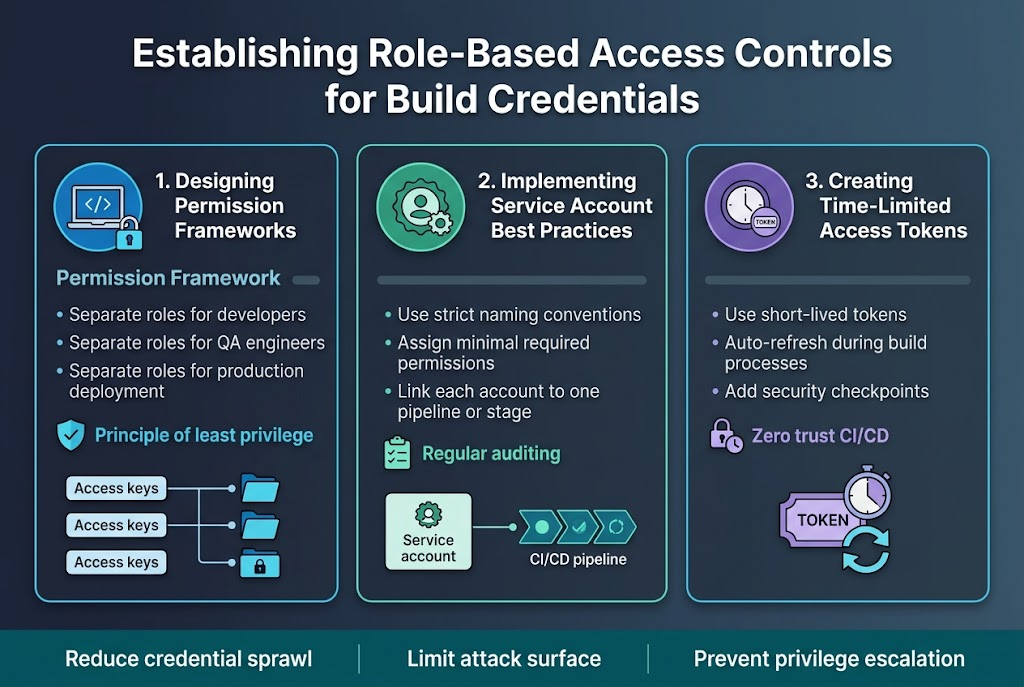
Effective role-based access control builds require carefully structured permission frameworks that limit credential access to specific job functions and environments. Organizations should implement principle of least privilege by creating distinct roles for developers, QA engineers, and production deployment processes, each with tailored access to necessary secrets only. This granular approach prevents credential sprawl and reduces the attack surface in automated build systems.
Implementing Service Account Best Practices
Service accounts dedicated to CI/CD security best practices should follow strict naming conventions and be assigned minimal required permissions for their specific tasks. Each service account must be linked to particular build pipelines or deployment stages, avoiding shared credentials across multiple processes. Regular auditing of service account permissions helps maintain secure credential management and prevents privilege escalation in build environments.
Creating Time-Limited Access Tokens
Token-based authentication with expiration windows significantly enhances automated build credentials security by reducing exposure time of sensitive information. Implementing short-lived tokens that automatically refresh during build processes creates multiple security checkpoints while maintaining operational efficiency. This approach aligns with zero trust CI/CD principles and provides additional protection against credential theft or misuse.
Adopting Zero-Trust Security Principles in CI/CD
Eliminating Hardcoded Credentials from Source Code
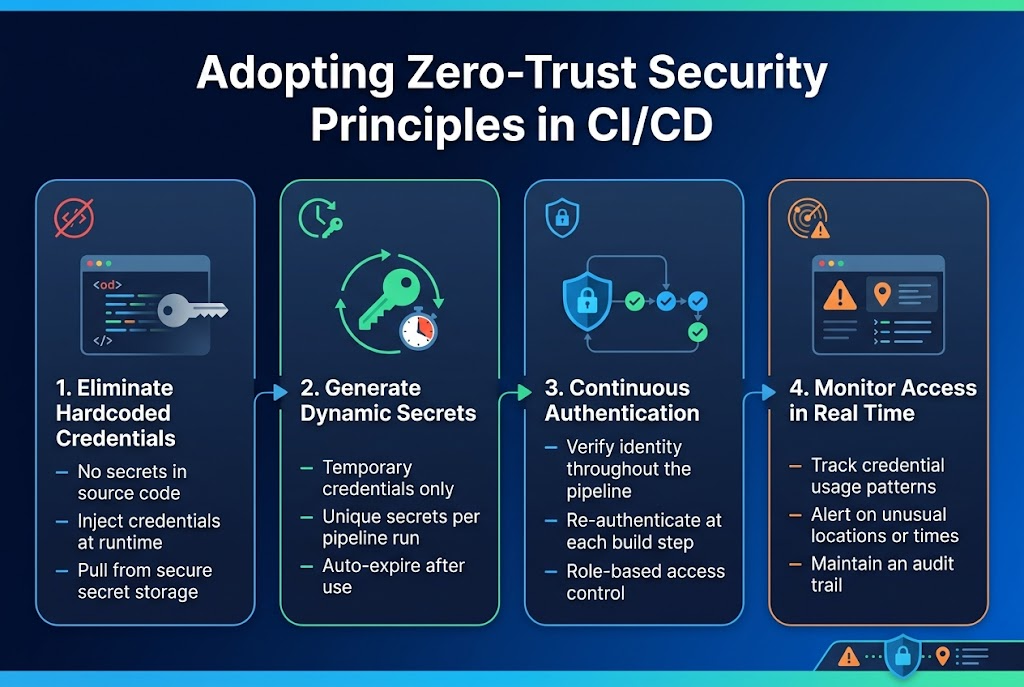
Hardcoded credentials in source code create massive security risks that can expose your entire build system to attackers. Modern zero trust CI/CD security demands dynamic credential injection at runtime rather than storing secrets directly in repositories. Build systems should pull credentials from secure secret storage solutions during execution, preventing accidental exposure through code commits or public repositories.
Implementing Dynamic Secret Generation
Dynamic secret generation creates temporary credentials with limited lifespans, reducing the attack window if credentials become compromised. This approach generates unique secrets for each build pipeline execution, automatically expiring them after use. CI/CD security best practices require implementing just-in-time credential provisioning that creates secrets only when needed and destroys them immediately after task completion.
Establishing Continuous Authentication Protocols
Continuous authentication validates build system identity throughout the entire pipeline execution, not just at initial login. Each build step must re-authenticate using role-based access control builds that verify permissions for specific actions. This ongoing verification process ensures that compromised credentials can’t be used beyond their intended scope, maintaining security even during long-running automated build processes.
Monitoring Real-Time Access Patterns
Real-time monitoring tracks credential usage patterns to detect anomalous behavior that might indicate security breaches. Automated build credentials should trigger alerts when accessed from unexpected locations, at unusual times, or for unauthorized resources. This monitoring creates an audit trail that helps security teams respond quickly to potential threats while ensuring legitimate build processes continue running smoothly.
Automating Credential Rotation and Lifecycle Management
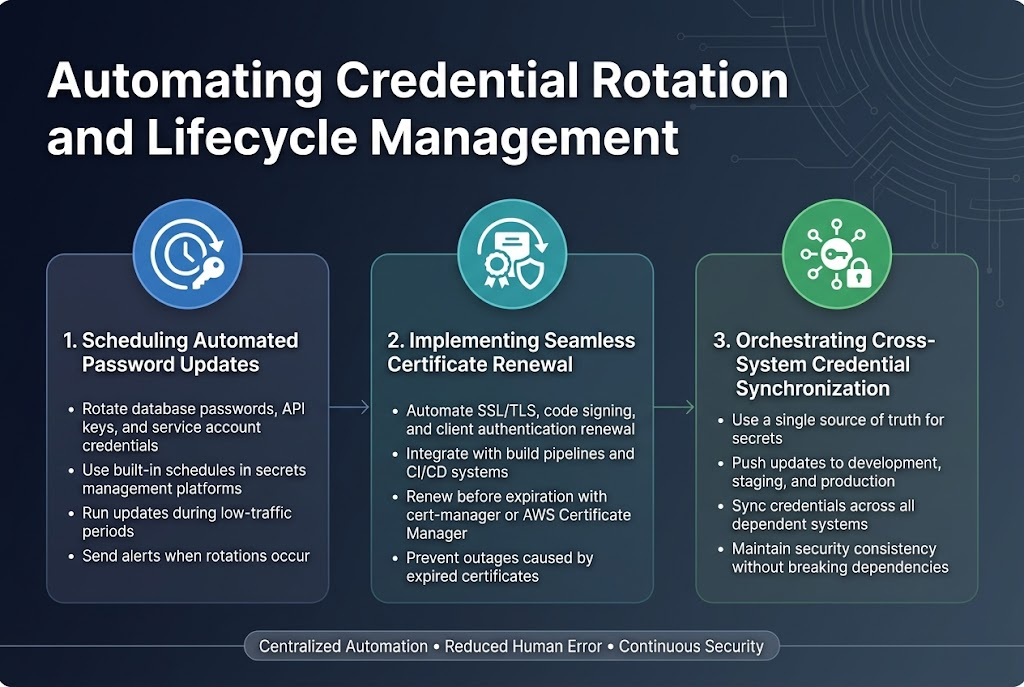
Scheduling Automated Password Updates
Automated password rotation is a cornerstone of credential rotation automation in modern DevOps environments. Most secrets management platforms offer built-in scheduling capabilities that allow teams to set rotation intervals based on security policies and compliance requirements. Setting up automated rotations for database passwords, API keys, and service account credentials eliminates the manual overhead while reducing human error risks. Configure rotation schedules during low-traffic periods to minimize service disruptions, and implement proper notification systems to alert teams when rotations occur.
Implementing Seamless Certificate Renewal
Certificate lifecycle management becomes critical as organizations scale their CI/CD security best practices. Automated certificate renewal systems should integrate with your existing build pipelines to handle SSL/TLS certificates, code signing certificates, and client authentication certificates. Tools like cert-manager for Kubernetes or AWS Certificate Manager can automatically renew certificates before expiration and update them across all dependent services. This approach prevents the dreaded certificate expiration incidents that can bring entire systems offline.
Orchestrating Cross-System Credential Synchronization
Modern applications often span multiple environments and platforms, making automated build credentials synchronization essential. Implement centralized secret distribution mechanisms that can push updated credentials to all dependent systems simultaneously. Use tools like HashiCorp Vault’s dynamic secrets or Azure Key Vault to create a single source of truth that automatically propagates changes across development, staging, and production environments. This orchestration ensures that credential updates don’t break service dependencies and maintains security consistency across your entire infrastructure.
Monitoring and Auditing Credential Usage Patterns
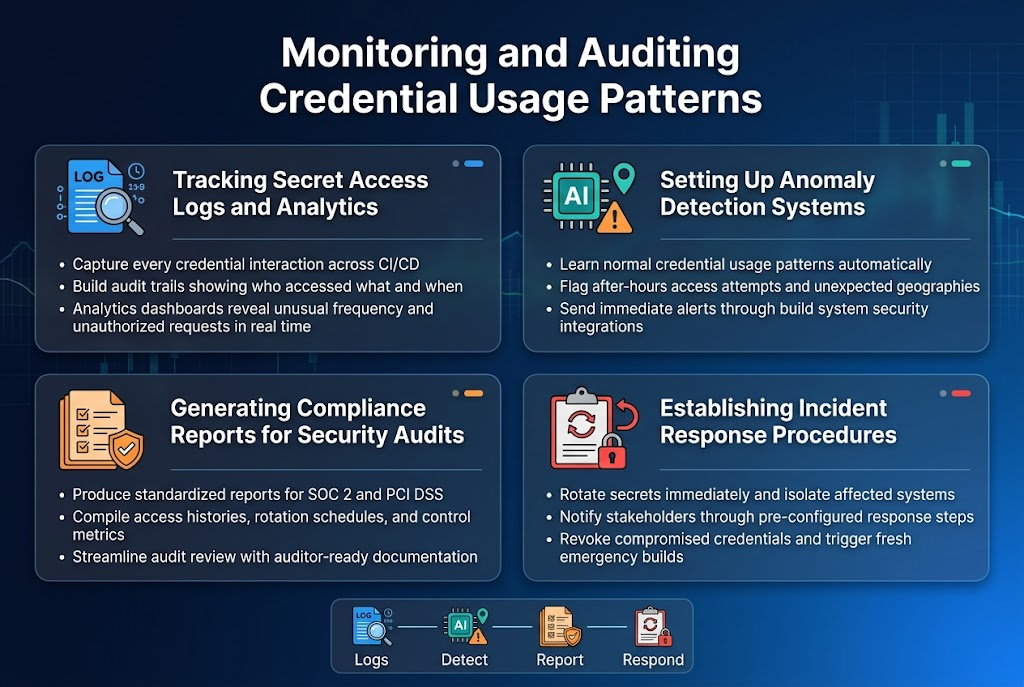
Tracking Secret Access Logs and Analytics
Comprehensive logging captures every credential interaction across your CI/CD pipeline, creating detailed audit trails that show who accessed what secrets and when. Modern secret management platforms provide built-in analytics dashboards that visualize usage patterns, helping security teams identify unusual access frequencies or unauthorized credential requests in real-time.
Setting Up Anomaly Detection Systems
Smart detection systems learn normal credential usage patterns and automatically flag suspicious activities like after-hours access attempts or credentials being used from unexpected geographic locations. These AI-powered tools integrate with existing build system security infrastructure to send immediate alerts when potential threats emerge.
Generating Compliance Reports for Security Audits
Automated reporting tools generate standardized compliance documentation that satisfies regulatory requirements like SOC 2 and PCI DSS. These reports compile credential access histories, rotation schedules, and security control effectiveness metrics into formats auditors expect, streamlining the compliance process.
Establishing Incident Response Procedures
Well-defined response procedures outline specific steps when credential compromise occurs, including immediate secret rotation, affected system isolation, and stakeholder notification protocols. Response teams use pre-configured playbooks that automatically revoke compromised credentials and trigger emergency builds with fresh secrets.
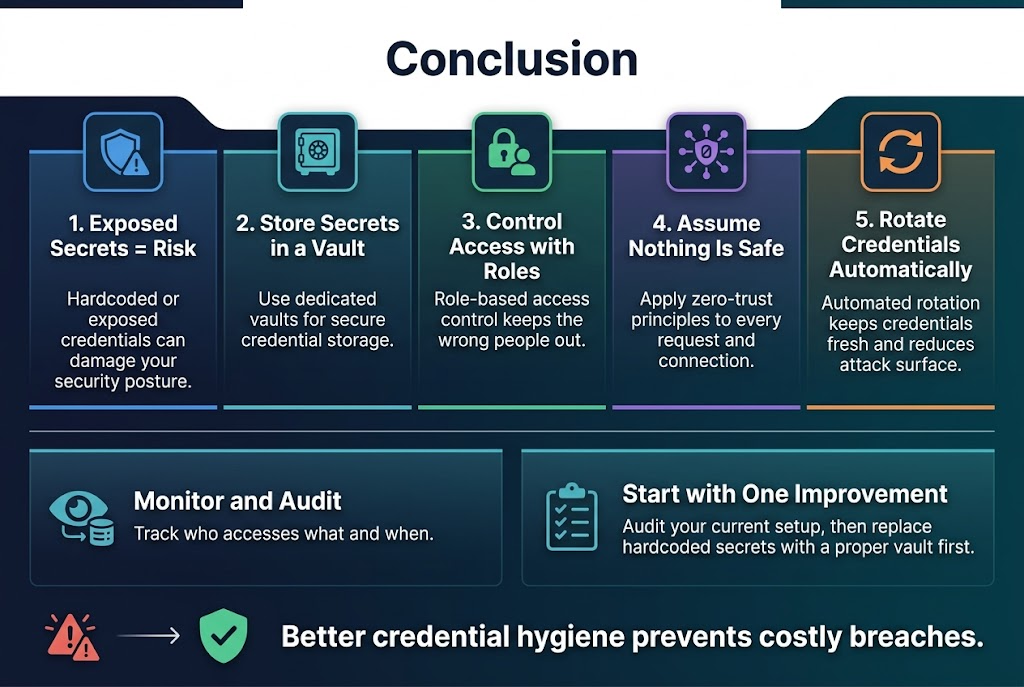
Managing credentials securely in your automated build systems isn’t just a nice-to-have anymore – it’s absolutely essential. We’ve covered how exposed secrets can wreck your security posture, explored solid storage solutions like dedicated vaults, and looked at how role-based access controls keep the wrong people away from sensitive data. Zero-trust principles help you assume nothing is safe by default, while automated rotation keeps your credentials fresh and your attack surface small.
The monitoring and auditing piece ties it all together by giving you visibility into who’s accessing what and when. Start by auditing your current setup to spot any glaring vulnerabilities, then pick one area to improve first – maybe switching from hardcoded secrets to a proper vault system. Your future self will thank you when you’re not scrambling to contain a breach that could have been prevented with better credential hygiene.




















