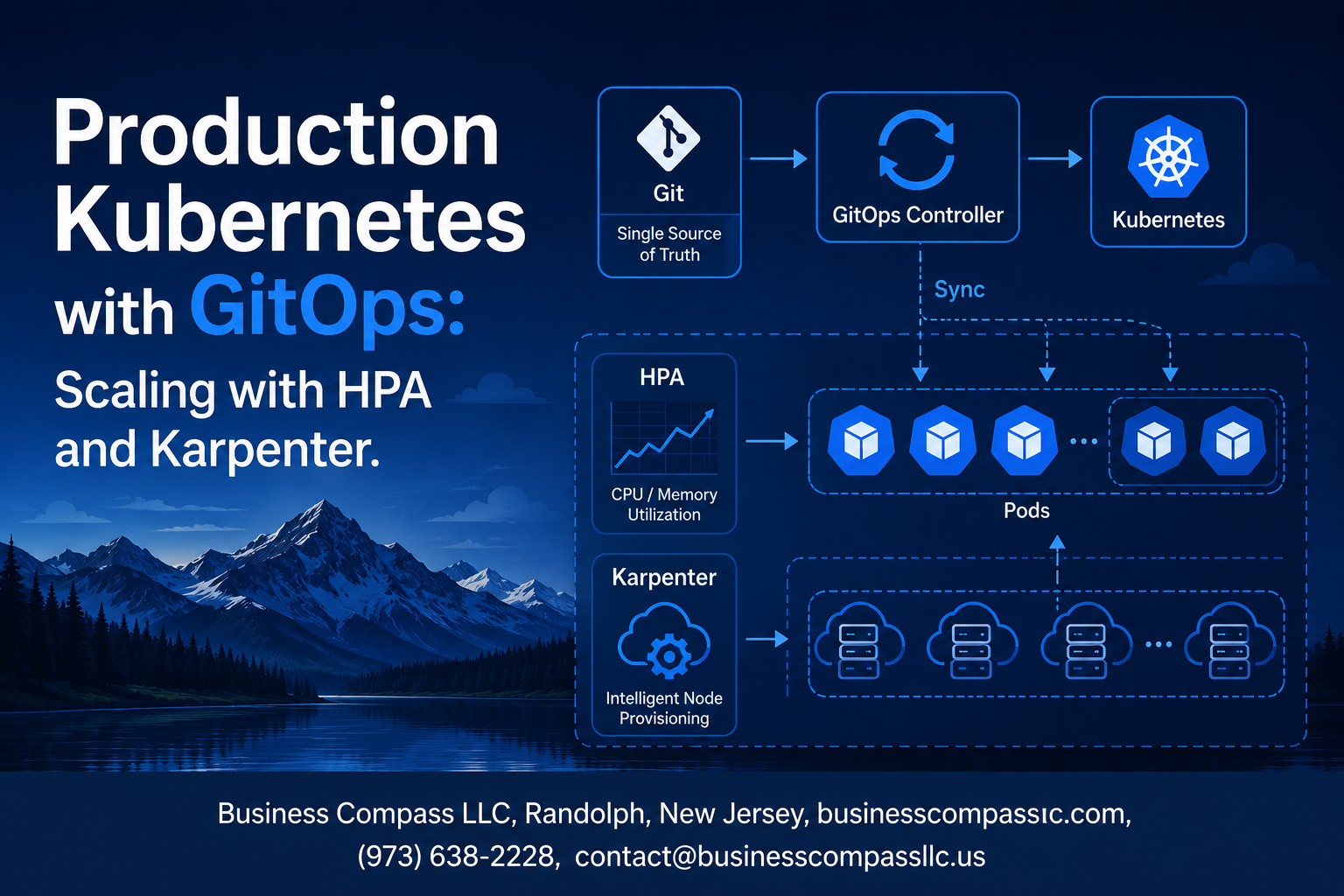
Production Kubernetes with GitOps: Scaling with HPA and Karpenter
Managing Production Kubernetes GitOps environments requires smart scaling strategies that balance performance with cost efficiency. This guide is designed for DevOps engineers, platform teams, and
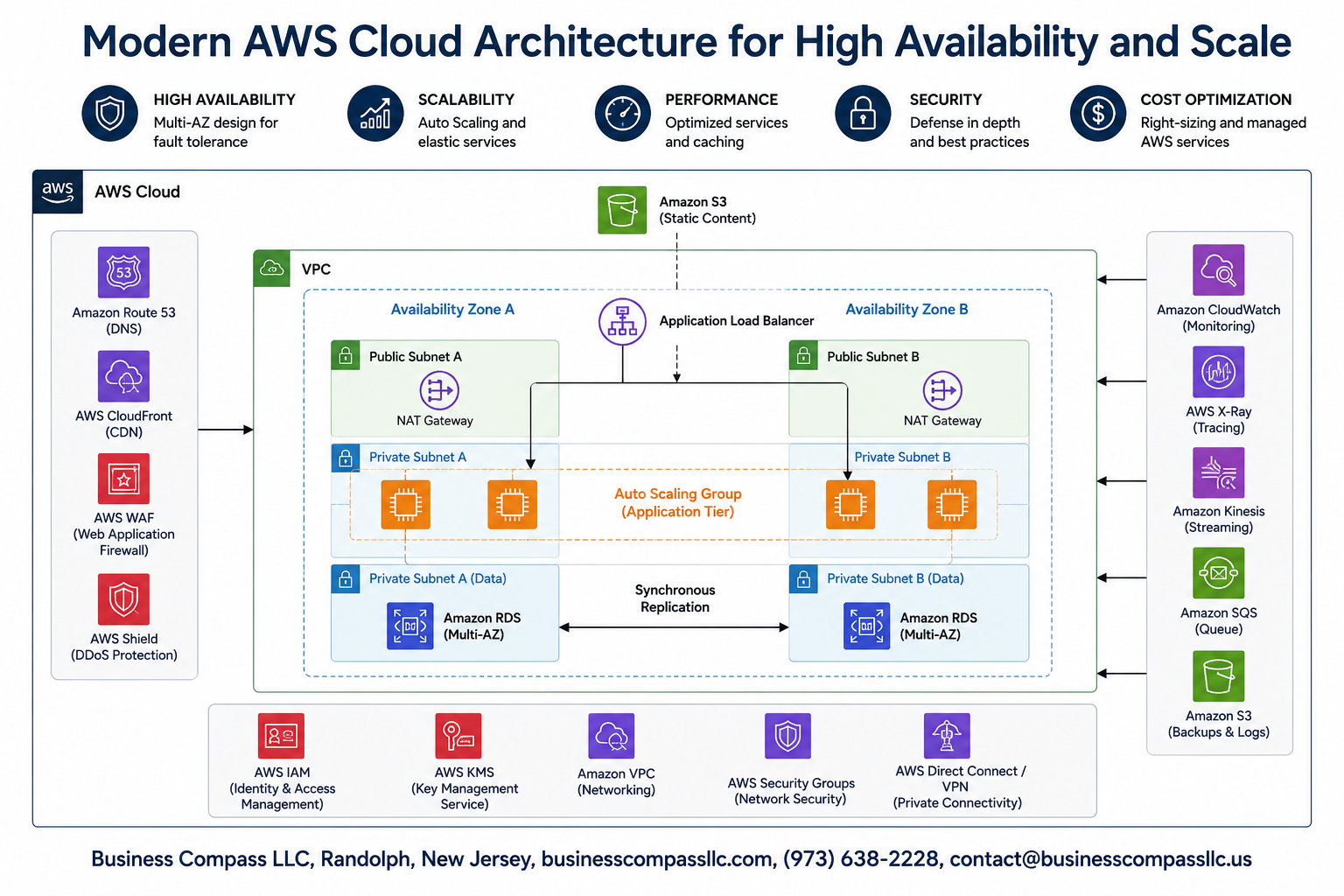
Modern AWS Cloud Architecture for High Availability and Scale
Building a robust AWS cloud architecture that stays online and handles traffic spikes is critical for modern businesses. When your applications go down or can’t

Building iOS Push Notifications on AWS SNS with a Custom Resource
iOS developers and DevOps engineers often struggle with setting up reliable push notifications that scale with their applications. Building iOS push notifications on AWS SNS
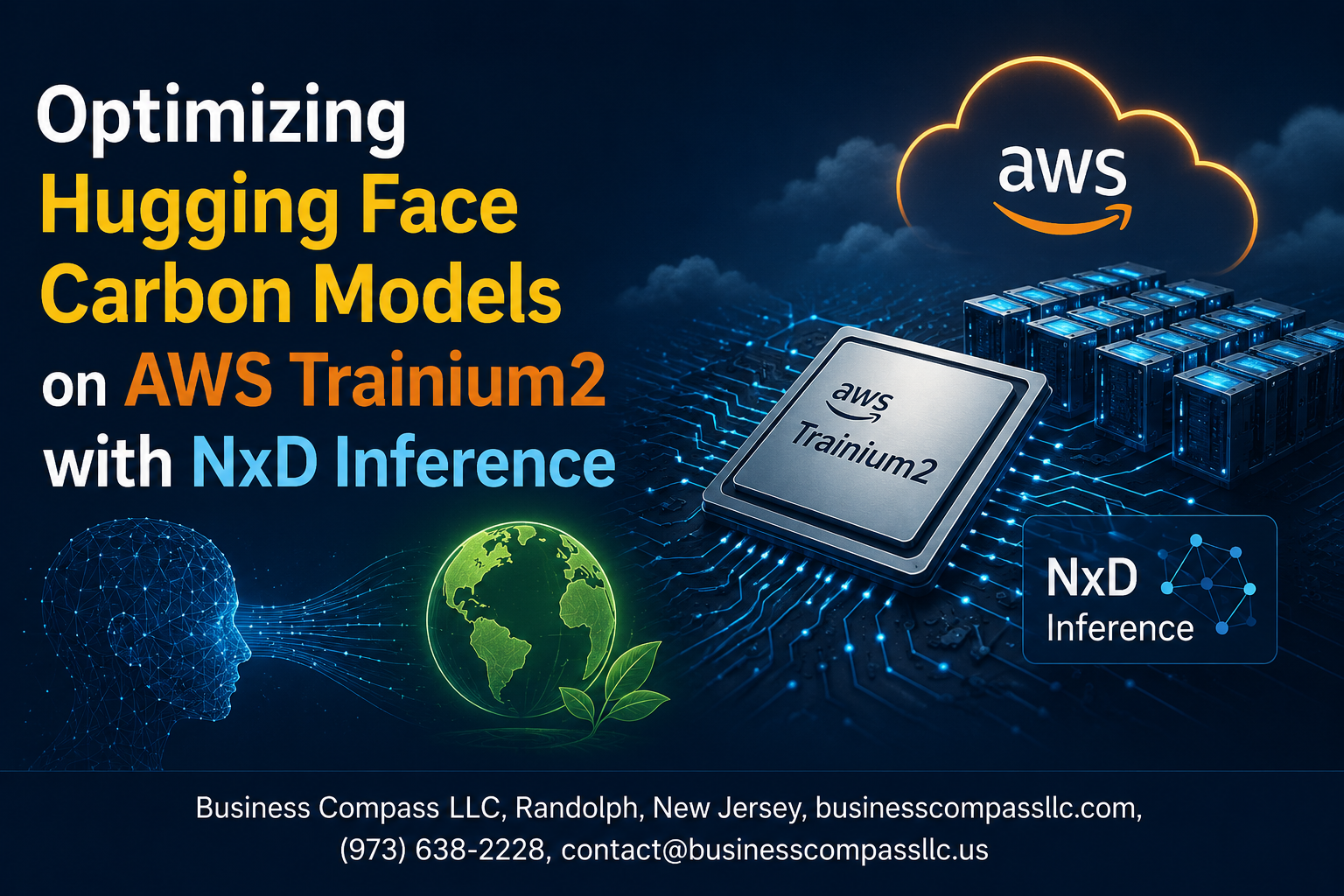
Optimizing Hugging Face Carbon Models on AWS Trainium2 with NxD Inference
Optimizing Hugging Face Carbon Models on AWS Trainium2 with NxD Inference Running large language models in production means dealing with sky-high costs and frustrating latency

AWS Pricing Deep Dive: Save More with the Right Compute Strategy
AWS cloud costs can quickly spiral out of control if you’re not paying attention to your compute strategy. This deep dive into AWS pricing optimization
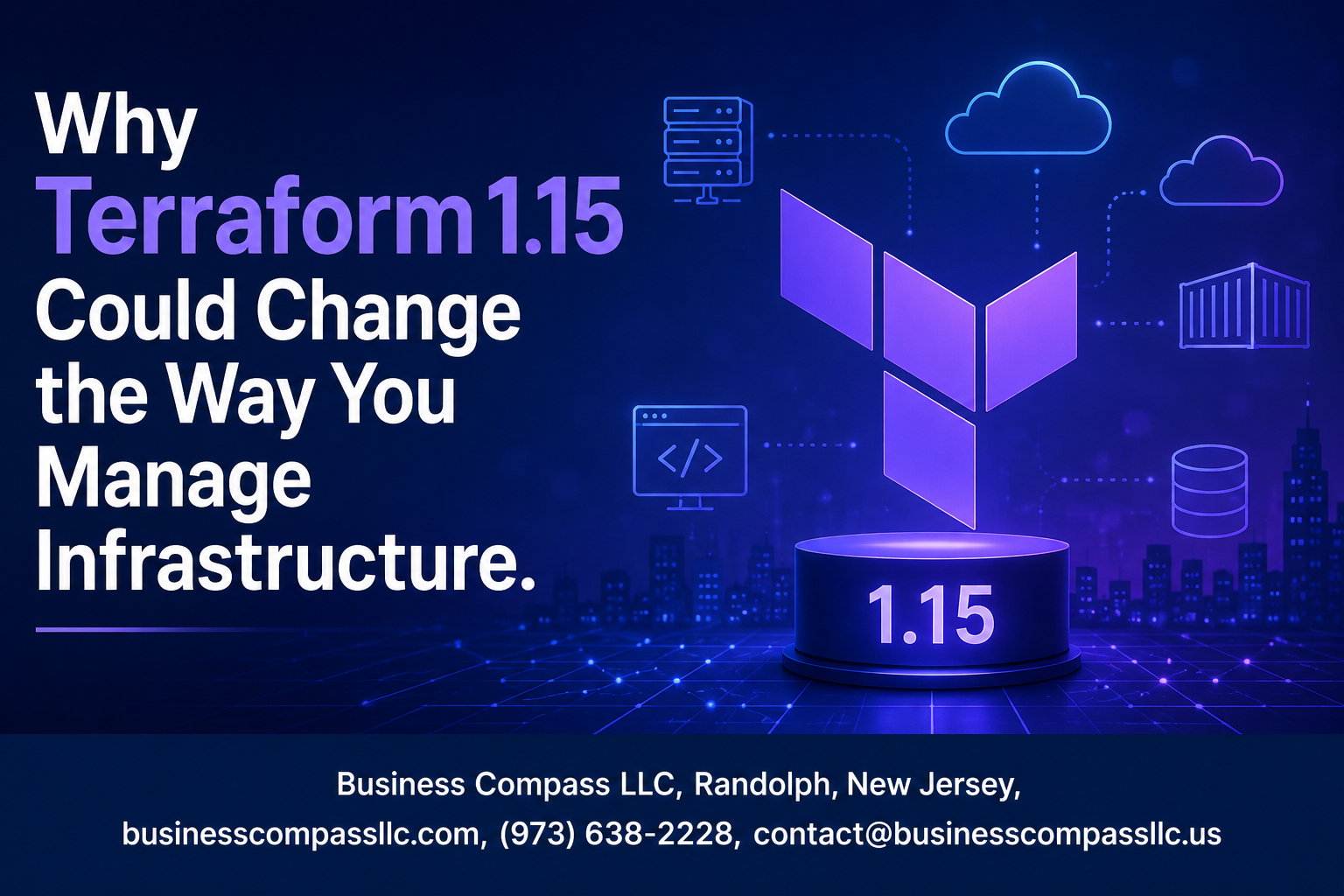
Why Terraform 1.15 Could Change the Way You Manage Infrastructure
Terraform 1.15 brings game-changing updates that could revolutionize how DevOps teams and infrastructure engineers handle infrastructure as code. This latest release introduces powerful Terraform features
The Real Economics of AWS Compute Savings Plans for Lambda and Fargate
AWS Compute Savings Plans can slash your Lambda and Fargate costs by up to 66%, but the actual savings depend on your usage patterns and
MyDocFind Architecture Deep Dive: HIPAA Compliance Meets Cloud Scalability
Healthcare organizations need robust data architecture that protects patient information while delivering fast, reliable performance. MyDocFind’s architecture tackles this challenge by combining HIPAA compliance with

How Snowflake Simplifies Production ML Inference at Scale
How Snowflake Simplifies Production ML Inference at Scale Machine learning teams at enterprise companies face a common challenge: deploying models that can handle thousands of

Building Enterprise AI with Claude on AWS: Architecture and Benefits
Enterprise teams are discovering that combining Claude AI enterprise capabilities with AWS AI architecture creates powerful business solutions. This guide is designed for IT leaders,









