Designing Scalable IAM Automation for Enterprises

Managing user identities and access across thousands of employees, contractors, and systems creates massive headaches for enterprise IT teams. Designing scalable IAM automation for enterprises solves this challenge by streamlining identity governance while maintaining security at scale. This guide targets IT architects, security engineers, and identity management professionals who need to build or improve enterprise […]
Deploying Redis Agent Memory Server on EC2 with Terraform
Setting up a high-performance Redis memory server on AWS EC2 doesn’t have to be complicated when you use Terraform to automate the entire process. This guide shows DevOps engineers, cloud architects, and backend developers how to deploy Redis on AWS EC2 with infrastructure-as-code practices that save time and reduce human error. You’ll learn to create […]
Amazon’s AI Strategy: The Next Evolution of Entertainment

Amazon is reshaping how we consume entertainment through cutting-edge Amazon AI strategy that goes far beyond basic recommendations. This transformation affects millions of viewers who use Amazon Prime Video AI and other entertainment platforms daily. This analysis is perfect for: Entertainment industry professionals, tech enthusiasts, streaming service users, and business leaders wanting to understand how […]
Cloud, Security, and Managed Services Trends Shaping the Future

Cloud, Security, and Managed Services Trends Shaping the Future The business technology landscape is changing fast. Companies everywhere are rethinking how they handle cloud computing trends, cybersecurity frameworks, and managed IT services to stay competitive and secure. This guide is for IT leaders, business executives, and technology decision-makers who need practical insights on the latest […]
Deploying Secure and Scalable CTF Environments on AWS
Running cybersecurity training competitions or educational programs? You need a rock-solid foundation that can handle hundreds of participants without breaking your budget or compromising security. This guide walks you through deploying secure CTF infrastructure on AWS that scales seamlessly from small workshops to massive competitions. This comprehensive resource is designed for cybersecurity educators, corporate training […]
Governance-First AI: Tracking Textract Usage Across AWS Accounts
Managing AWS Textract governance across multiple accounts can feel like herding cats—especially when you’re dealing with dozens of teams extracting data from documents without clear visibility into costs or usage patterns. This guide is for AWS architects, cloud engineers, and IT leaders who need to establish control over their organization’s document processing operations while keeping […]
Grafana Loki Promtail Prometheus Stack for Kubernetes Observability
Kubernetes observability becomes critical when managing complex containerized environments at scale. The Grafana Loki Promtail stack combined with Prometheus monitoring Kubernetes creates a powerful solution for tracking application performance, troubleshooting issues, and maintaining system health. This guide targets DevOps engineers, SRE teams, and platform administrators who need to implement comprehensive monitoring and logging across their […]
NAT Gateway vs Internet Gateway: Understanding Secure Traffic Flow
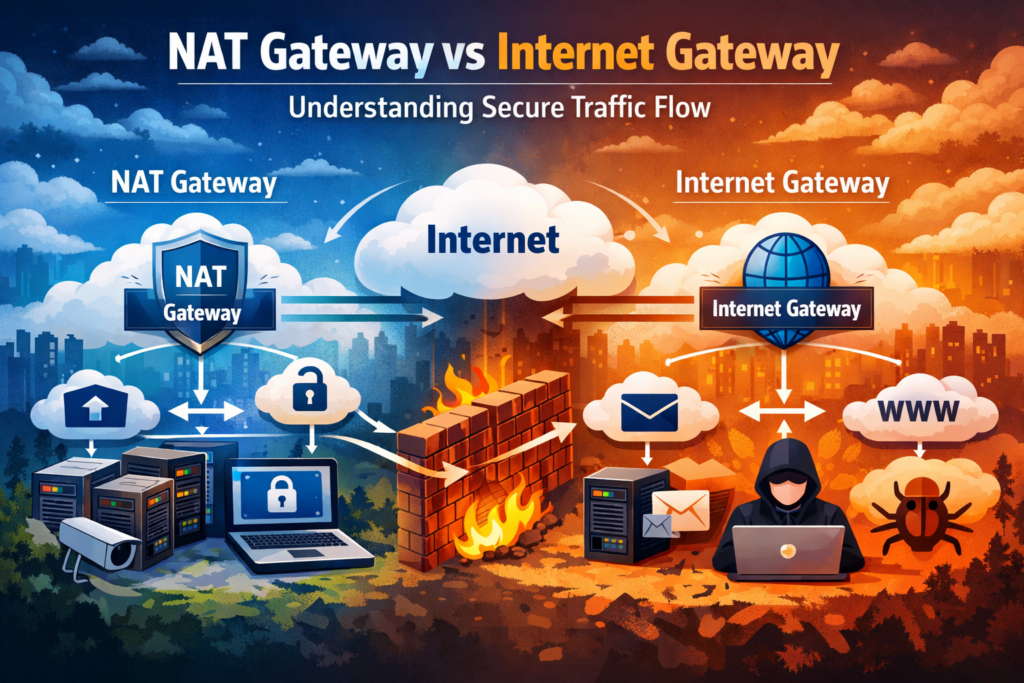
When building secure AWS cloud infrastructure, choosing between a NAT Gateway vs Internet Gateway can make or break your network security strategy. These two critical components handle traffic differently, and picking the wrong one could expose your resources or inflate your costs. This guide is designed for cloud architects, DevOps engineers, and AWS practitioners who […]
Optimizing Data Storage Costs with Amazon S3 Storage Classes
Amazon S3 storage costs can quickly spiral out of control without the right strategy. This guide is designed for cloud architects, DevOps engineers, and IT professionals who want to slash their AWS storage bills while maintaining performance and accessibility. You’ll discover how to choose the right Amazon S3 storage classes based on your data access […]
Designing a Secure AWS Lightsail Architecture
AWS Lightsail offers an accessible entry point into cloud computing, but many developers and small business owners overlook critical security measures that protect their applications and data. This guide targets developers, startup founders, and IT professionals who want to build a secure Lightsail architecture without getting overwhelmed by complex enterprise solutions. Security isn’t just about […]









