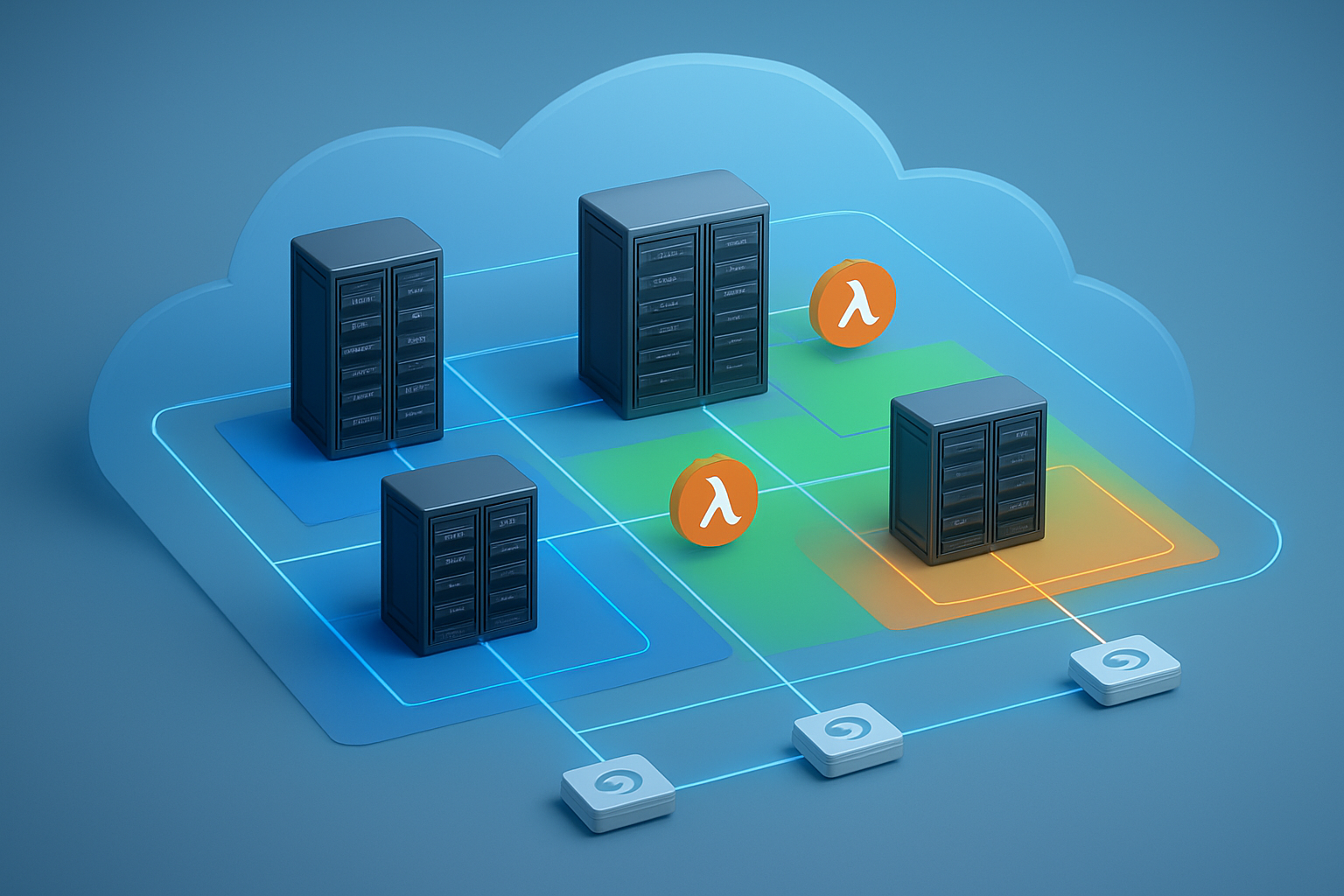
AWS Lambda availability zones can make or break your serverless application’s reliability. When your Lambda functions run across multiple zones, they stay up even when individual data centers go down – but getting this right requires more than just hoping AWS handles everything for you.
This guide is for cloud engineers, DevOps teams, and solution architects who want to build rock-solid serverless applications that don’t crumble during outages. You’ll learn how to design AZ-aware serverless applications that keep running when things go wrong, without breaking the bank.
We’ll walk through designing Lambda functions for multi-AZ resilience so your code automatically spreads across availability zones. You’ll also discover database integration strategies that keep your data accessible from any zone, plus monitoring and observability techniques that help you spot issues before users do. Ready to build serverless apps that actually stay up when it matters most?
Understanding Availability Zones and Their Impact on Serverless Architecture

Define AWS Availability Zones and their role in fault tolerance
AWS Availability Zones represent physically isolated data centers within a region, each with independent power, cooling, and networking infrastructure. These zones are strategically positioned to prevent cascading failures while maintaining low-latency connections between zones. When building AWS Lambda availability zones architecture, each AZ operates as an independent failure domain, meaning an outage in one zone won’t directly impact resources in another.
AWS Lambda fault tolerance depends heavily on this multi-AZ foundation. Lambda automatically distributes function executions across available zones within a region, but this default behavior doesn’t guarantee your application will gracefully handle zone-level failures. Smart architects design their serverless multi-AZ architecture with deliberate redundancy patterns that account for potential zone unavailability.
Explore how Lambda functions interact with AZ infrastructure
Lambda functions run on AWS-managed infrastructure that spans multiple availability zones by default. When you invoke a function, AWS routes the request to available compute capacity across zones based on current load and resource availability. This distribution happens transparently, but the underlying AZ placement becomes critical when your Lambda functions interact with VPC-bound resources like databases or custom networking configurations.
Lambda VPC configuration creates direct dependencies on specific AZ resources. Functions configured with VPC access require subnet assignments, and these subnets exist within particular availability zones. If your function needs to connect to an RDS instance in a specific AZ, network latency and potential cross-AZ data transfer costs become important considerations for your AZ-aware serverless applications.
Identify common pitfalls when ignoring AZ considerations
Single-AZ database deployments create the most dangerous vulnerability in serverless architectures. Developers often provision RDS instances or other data stores in just one availability zone to save costs, unknowingly creating a single point of failure that can bring down their entire application. When that zone experiences issues, Lambda functions can’t reach critical data stores, causing widespread service disruption.
Hardcoded resource references represent another frequent mistake. Applications that assume specific AZ placement for resources like EFS mount targets or ElastiCache clusters break when AWS redistributes Lambda execution to different zones. AWS Lambda resilience requires designing applications that can discover and connect to resources dynamically rather than relying on fixed AZ assumptions.
Analyze the performance implications of AZ-unaware designs
Cross-AZ network calls introduce measurable latency overhead, typically adding 1-2 milliseconds per hop compared to intra-AZ communication. For Lambda functions making multiple database queries or API calls, these milliseconds compound quickly. Applications that ignore AZ placement might experience inconsistent response times as AWS balances Lambda execution across different zones relative to their data sources.
Data transfer costs also escalate with AZ-unaware designs. AWS charges for data movement between availability zones, and chatty applications can accumulate significant expenses. Functions that pull large datasets from cross-AZ resources face both performance penalties and unexpected billing. Multi-zone Lambda deployment strategies should minimize these cross-AZ interactions through intelligent resource placement and caching patterns.
Designing Lambda Functions for Multi-AZ Resilience

Implement proper error handling and retry mechanisms
Building robust AWS Lambda resilience requires implementing exponential backoff strategies and circuit breaker patterns. Lambda functions should catch AZ-specific failures and automatically retry operations with increasing delays, preventing cascade failures across availability zones. Configure dead letter queues to capture failed invocations and implement custom retry logic that accounts for cross-zone latency variations.
Configure function timeouts for cross-AZ operations
Cross-AZ network calls introduce additional latency that demands careful timeout configuration. Set Lambda function timeouts 20-30% higher than single-AZ operations to accommodate inter-zone communication delays. Database connections and API calls spanning availability zones need generous timeout buffers while maintaining reasonable user experience thresholds.
Optimize memory allocation for consistent performance across zones
Memory allocation directly impacts CPU performance and network throughput in Lambda functions. Allocate sufficient memory (minimum 1024MB) for multi-AZ applications to ensure consistent processing power across different availability zones. Higher memory configurations provide better network performance for cross-zone operations and reduce cold start times that affect AZ-aware serverless applications.
Leveraging VPC Configuration for AZ-Aware Lambda Deployments
Set up subnet configurations across multiple availability zones
Designing subnets across multiple availability zones requires careful planning to ensure your AWS Lambda VPC configuration supports true fault tolerance. Create at least two private subnets in separate AZs, with each subnet using distinct CIDR blocks from your VPC’s address space. This approach allows Lambda functions to fail over between zones when AZ-level outages occur. Include public subnets in each AZ to host NAT Gateways or NAT instances for outbound internet connectivity.
Configure security groups for cross-AZ communication
Security groups act as virtual firewalls that control traffic flow between Lambda functions and other AWS resources across availability zones. Design security groups with rules that permit communication between subnets in different AZs, especially for database connections and inter-service communication. Create separate security groups for different application tiers – one for Lambda functions, another for databases, and additional groups for any intermediate services. Reference security groups by ID rather than CIDR blocks to maintain flexibility as your serverless multi-AZ architecture evolves.
Implement NAT Gateway strategies for outbound connectivity
NAT Gateways provide essential outbound internet access for Lambda functions deployed in private subnets while maintaining security. Deploy one NAT Gateway per availability zone to eliminate single points of failure and reduce cross-AZ data transfer charges. Configure route tables to direct traffic from each private subnet to its corresponding AZ’s NAT Gateway. This strategy ensures Lambda functions maintain internet connectivity even during AZ-level NAT Gateway failures and optimizes costs by avoiding inter-AZ traffic for routine outbound requests.
Monitor VPC endpoint performance across zones
VPC endpoints enable private connectivity to AWS services without routing traffic through the internet, making them crucial for AZ-aware serverless applications. Deploy interface endpoints across multiple availability zones to ensure consistent performance and availability. Monitor endpoint metrics like request latency, error rates, and throughput using CloudWatch to identify performance bottlenecks. Gateway endpoints for S3 and DynamoDB automatically distribute across AZs, but you should still track their performance to optimize your Lambda functions’ data access patterns.
Database Integration Strategies for Multi-AZ Lambda Applications

Connect Lambda functions to RDS Multi-AZ deployments
Connecting your AWS Lambda functions to RDS Multi-AZ deployments creates a robust foundation for serverless database integration strategies. Multi-AZ RDS automatically handles failover between availability zones, ensuring your Lambda functions maintain database connectivity even during zone outages. Configure your Lambda functions within the same VPC as your RDS instances, using security groups to control access while enabling seamless communication across availability zones.
Implement DynamoDB Global Tables for cross-region redundancy
DynamoDB Global Tables extend multi-AZ architecture beyond single regions, providing automatic replication across multiple AWS regions. Your Lambda functions can read from local replicas while writes propagate globally, reducing latency and improving fault tolerance. Enable point-in-time recovery and configure consistent read settings to balance performance with data consistency requirements across your distributed serverless applications.
Configure connection pooling for database efficiency
Connection pooling dramatically improves database efficiency in multi-zone Lambda deployment scenarios. Use RDS Proxy to manage database connections across availability zones, reducing connection overhead and enabling better resource utilization. RDS Proxy handles connection multiplexing automatically, allowing thousands of Lambda functions to share a smaller pool of database connections while maintaining security through IAM authentication.
Handle database failover scenarios gracefully
Graceful failover handling requires implementing retry logic and circuit breaker patterns in your Lambda functions. Configure exponential backoff strategies to manage temporary connectivity issues during AZ transitions. Monitor database health endpoints and implement fallback mechanisms that can redirect traffic to healthy availability zones, ensuring your serverless multi-AZ architecture maintains service continuity during infrastructure disruptions.
Monitoring and Observability for AZ-Distributed Lambda Functions

Set up CloudWatch metrics for AZ-specific performance tracking
Monitor your Lambda monitoring observability across availability zones by creating custom CloudWatch metrics that track function execution per AZ. Configure dimension filters to segment performance data by availability zone, enabling precise identification of zone-specific bottlenecks or failures. Set up metric streams to capture invocation counts, duration, and error rates for each AZ where your functions execute.
Implement distributed tracing with AWS X-Ray
AWS X-Ray provides comprehensive tracing for serverless multi-AZ architecture by tracking requests as they flow between Lambda functions and other AWS services across different availability zones. Enable X-Ray tracing on your Lambda functions to visualize the complete request path, identify cross-AZ latency patterns, and pinpoint performance issues in specific zones.
Create custom dashboards for multi-AZ health monitoring
Build CloudWatch dashboards that display real-time health metrics for your AZ-aware serverless applications. Include widgets showing per-zone error rates, latency distributions, and resource utilization patterns. Design dashboard layouts that highlight zone-specific anomalies and provide quick access to troubleshooting data for operations teams.
Configure automated alerts for AZ-related failures
Establish CloudWatch alarms that trigger when availability zone-specific thresholds are breached. Set up automated notifications for scenarios like elevated error rates in a single AZ, unusual latency spikes, or complete zone unavailability. Configure alarm actions to automatically failover traffic or scale resources in healthy zones when failures are detected.
Cost Optimization Techniques for Multi-AZ Serverless Applications

Analyze data transfer costs between availability zones
Data transfer charges can quietly drain your AWS bill when Lambda functions communicate across availability zones. AWS charges $0.01 per GB for cross-AZ data transfer, which accumulates rapidly in high-throughput serverless applications. Monitor your CloudWatch metrics to identify Lambda functions generating excessive inter-AZ traffic and consider architectural changes to reduce these costs.
Optimize Lambda function placement to minimize cross-AZ calls
Strategic placement of Lambda functions near their data sources dramatically reduces both latency and AWS Lambda costs. Deploy functions in the same availability zone as your RDS instances or ElastiCache clusters whenever possible. Use Lambda layers to share common code across multiple AZ deployments, avoiding duplication while maintaining proximity to resources.
Implement intelligent routing to reduce latency and costs
Smart routing algorithms can automatically direct requests to the most cost-effective availability zone based on current load and data locality. Implement Application Load Balancer rules that consider both response times and data transfer costs when distributing traffic. This serverless cost optimization approach ensures your multi-AZ Lambda deployment maintains performance while minimizing unnecessary cross-zone communications.

Building serverless applications that work across multiple availability zones isn’t just about checking a box for high availability – it’s about creating systems that your users can count on, even when things go wrong. By designing your Lambda functions with multi-AZ resilience in mind, configuring your VPCs thoughtfully, and connecting to databases that can handle zone failures, you’re setting up your applications to keep running smoothly no matter what happens behind the scenes.
The real magic happens when you combine solid monitoring with smart cost optimization. Keep an eye on how your functions perform across different zones, and don’t be afraid to adjust your setup based on what the data tells you. Your future self (and your users) will thank you for taking the time to build these resilient, zone-aware applications that can handle whatever AWS throws at them.