Setting up OpenID Connect AWS authentication can transform how your team accesses cloud resources, but the configuration process often feels overwhelming. This comprehensive guide walks you through implementing AWS Identity Center OIDC and AWS IAM OpenID Connect integration from start to finish.
This tutorial is designed for cloud engineers, DevOps professionals, and IT administrators who need to implement secure, scalable authentication for their AWS environments. No matter if you’re migrating from traditional authentication methods or setting up OIDC implementation AWS for the first time, you’ll find practical, tested solutions here.
We’ll cover the essential OpenID Connect configuration AWS fundamentals you need to understand before diving into implementation. You’ll learn how to properly set up AWS Identity Center setup with external identity providers, including detailed configuration steps and real-world examples. Finally, we’ll explore security best practices and troubleshooting techniques to ensure your OIDC authentication AWS deployment runs smoothly in production.
By the end of this guide, you’ll have a working AWS SSO OpenID Connect implementation that your users can rely on for seamless, secure access to your AWS resources.
Understanding OpenID Connect Fundamentals for AWS Integration
Core OpenID Connect protocol components and authentication flow
OpenID Connect AWS integration relies on three key components: the Identity Provider (IdP), the Relying Party (AWS services), and the end user. The authentication flow begins when users access AWS resources, triggering a redirect to your external IdP for credential verification. After successful authentication, the IdP returns an ID token containing user claims and an authorization code. AWS IAM OpenID Connect then validates these tokens using JSON Web Key Sets (JWKS) and established trust relationships. This seamless process eliminates the need for users to maintain separate AWS credentials while ensuring secure access through established identity standards.
Benefits of implementing OIDC with AWS services
AWS Identity Center OIDC implementation transforms how organizations manage user access across their cloud infrastructure. Users enjoy single sign-on capabilities, accessing multiple AWS accounts and applications with one set of credentials from their familiar corporate identity provider. Organizations reduce administrative overhead by centralizing user management in existing directory services like Azure AD or Okta. Security improves through centralized policy enforcement, multi-factor authentication, and real-time user provisioning and deprovisioning. Cost optimization occurs as companies eliminate redundant identity systems and reduce support tickets related to password resets and account management across different AWS environments.
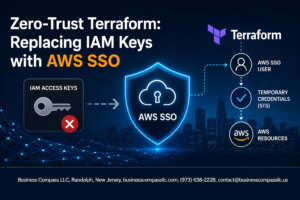
Key differences between OIDC and traditional AWS authentication methods
Traditional AWS authentication relies on long-term access keys, IAM users, and role assumptions that create security risks and management complexity. OpenID Connect configuration AWS shifts this paradigm by providing temporary, token-based authentication that automatically expires. While conventional methods require manual user creation and permission assignment in each AWS account, OIDC authentication AWS enables dynamic role mapping based on group memberships from your identity provider. Traditional approaches lack centralized logout capabilities, whereas AWS SSO OpenID Connect provides session management across all connected applications. The token-based approach also provides detailed user attributes and group information that can drive sophisticated authorization decisions within AWS services.
Setting Up AWS IAM for OpenID Connect Integration
Creating and configuring IAM identity providers for OIDC
AWS IAM identity providers act as bridges between your external OpenID Connect provider and AWS resources. Navigate to the IAM console and select “Identity providers” to create a new OIDC provider. You’ll need your identity provider’s issuer URL (typically found in the .well-known/openid_configuration endpoint) and the audience value that identifies your application. The thumbprint verification ensures secure communication by validating SSL certificates from your OIDC provider.
Establishing trust relationships between external providers and AWS
Trust relationships define which external identities can assume AWS roles through OpenID Connect authentication. Create trust policies that specify your OIDC provider’s ARN and include conditions that validate specific claims like audience, subject, or custom attributes. These conditions act as gatekeepers, ensuring only authenticated users from your organization can access AWS resources. The trust policy structure follows JSON format with principals, conditions, and actions clearly defined.
Defining IAM roles with appropriate permissions for OIDC users
Design IAM roles that align with your users’ job functions and security requirements. Each role should follow the principle of least privilege, granting only necessary permissions for specific tasks. Create separate roles for different user groups – developers might need EC2 and S3 access, while data analysts require access to Redshift and Athena. Attach managed policies or create custom policies that reflect your organization’s access patterns and compliance requirements.
Configuring role assumption policies for secure access
Role assumption policies control how and when external identities can assume your IAM roles. Configure session duration limits, MFA requirements, and IP address restrictions to enhance security. Use condition keys like StringEquals and StringLike to match specific claim values from your OIDC token. Set up session tags that carry user attributes from your identity provider into AWS, enabling fine-grained access control and audit trails across your infrastructure.
Implementing AWS Identity Center with OpenID Connect
Enabling Identity Center and selecting OIDC as external identity source
Start by navigating to the AWS Identity Center console and clicking “Enable Identity Center” if it’s your first setup. Once enabled, head to the Settings section and select “Identity source.” Choose “External identity provider” from the available options, then select “OpenID Connect” as your authentication method. This configuration tells AWS Identity Center to trust your external OIDC provider for user authentication instead of managing identities internally.
Configuring attribute mappings between identity provider and AWS
Map user attributes from your OpenID Connect provider to AWS Identity Center fields to ensure proper user profile creation. Access the attribute mappings section and configure essential mappings like email, firstName, lastName, and any custom attributes your organization uses. The standard OIDC claims typically include “sub” for user ID, “email” for email address, and “given_name” and “family_name” for user names. Set up group mappings by connecting your identity provider’s group claims to AWS Identity Center permission sets, enabling automatic access control based on group membership.
Setting up automatic user provisioning and group synchronization
Enable automatic provisioning in the SCIM configuration section to streamline user lifecycle management. Configure your OpenID Connect provider to send SCIM requests to the AWS Identity Center SCIM endpoint when users are created, modified, or deleted. Set up group synchronization by mapping your identity provider groups to AWS Identity Center groups, allowing automatic permission set assignments based on group membership. Configure provisioning filters to control which users get provisioned and establish sync schedules for regular updates.
Configuring Your External Identity Provider
Registering AWS as a relying party in your identity provider
Register AWS as a trusted application in your external identity provider by creating a new OIDC application or client configuration. Enter your AWS Identity Center instance ARN as the client identifier and configure the application type as confidential client. Most identity providers require you to specify the application name, description, and grant types – select authorization code flow for AWS integration. Generate client credentials securely and store the client ID and client secret for later AWS configuration steps.
Setting up required claims and scopes for AWS integration
Configure your identity provider to include essential claims in the ID token for AWS Identity Center OIDC integration. Map user attributes like email, name, groups, and department to standard OIDC claims such as email, name, groups, and custom:department. Enable the openid, profile, and email scopes at minimum, with additional custom scopes based on your attribute mapping requirements. Set up group membership claims if you plan to use group-based access control in AWS, ensuring group names match your AWS permission sets.
Configuring callback URLs and security parameters
Add your AWS Identity Center ACS (Assertion Consumer Service) URL to the allowed redirect URIs in your identity provider configuration. The callback URL typically follows the pattern https://portal.sso.region.amazonaws.com/saml/assertion/instance-id. Configure the token endpoint authentication method to client secret post or client secret basic depending on your provider’s capabilities. Set token expiration times appropriately – ID tokens should expire within 1 hour while refresh tokens can have longer lifespans based on your security requirements.
Testing identity provider connectivity and token issuance
Validate your OIDC configuration by testing the authorization flow manually using tools like curl or Postman to verify token issuance. Check that your identity provider’s well-known configuration endpoint returns valid metadata including authorization, token, and userinfo endpoints. Test user authentication flows to confirm that ID tokens contain the required claims with correct values. Monitor your identity provider logs during testing to identify any configuration issues or claim mapping problems before connecting to AWS Identity Center.
Step-by-Step Implementation Process
Connecting your identity provider to AWS Identity Center
Begin by navigating to AWS Identity Center and selecting “External identity source” from the settings. Enter your OpenID Connect provider’s metadata URL or manually configure endpoints including authorization, token, and userinfo URLs. AWS Identity Center OIDC integration requires specific scopes like openid, email, and profile. Configure attribute mappings to synchronize user identities correctly between your external provider and AWS, ensuring proper user identification and group membership propagation.
Mapping external groups to AWS permission sets
Create permission sets that define what resources users can access across your AWS accounts. Map external identity provider groups to these permission sets using the attribute-based access control (ABAC) feature. For example, map your “DevOps-Team” group from your identity provider to a permission set with EC2 and CloudFormation access. This OpenID Connect AWS configuration enables automatic permission inheritance based on group membership, reducing manual user management overhead while maintaining security boundaries.
Assigning users and groups to AWS accounts and roles
Access the AWS Identity Center dashboard and select specific AWS accounts where your users need access. Assign your mapped groups to these accounts with their corresponding permission sets. Users inherit permissions automatically when they authenticate through your OIDC authentication AWS setup. Create multiple assignments for different environments – development teams might access dev accounts while administrators get production access. This granular assignment ensures users only access resources they need for their specific roles and responsibilities.
Validating user authentication and authorization flow
Test the complete AWS SSO OpenID Connect flow by having users log in through your identity provider’s portal. Verify that authentication redirects properly to AWS Identity Center and that users can access assigned AWS accounts through the AWS access portal. Check CloudTrail logs to confirm successful authentication events and validate that users can assume only their designated roles. Monitor failed login attempts and permission errors to identify configuration issues early in your OpenID Connect implementation AWS deployment.
Testing and Troubleshooting Your OIDC Implementation
Verifying successful user authentication and role assumption
Start by confirming users can successfully log in through your external identity provider and receive the correct AWS credentials. Check that the authentication flow redirects properly to AWS and that users see their expected resources. Test role assumption by having authenticated users access AWS services specific to their assigned roles – they should only reach resources matching their permissions. Monitor the AWS CloudTrail logs to verify successful AssumeRoleWithWebIdentity API calls, which indicate proper OIDC token validation and role assumption.
Common configuration errors and their solutions
Mismatched audience claims between your identity provider and AWS IAM identity provider configuration frequently cause authentication failures. Double-check that the audience value in your OIDC tokens exactly matches what you specified in the AWS IAM identity provider settings. Trust relationship policies often contain syntax errors or incorrect condition statements – verify your condition blocks use the correct OIDC claim names and values. Certificate issues arise when the identity provider’s signing certificate changes without updating the AWS configuration. Role mapping problems occur when the OIDC token claims don’t match the conditions in your trust policies, so validate your claim mappings carefully.
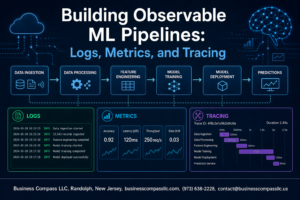
Monitoring authentication logs and debugging failed attempts
Enable AWS CloudTrail logging to capture all authentication attempts and API calls related to your OpenID Connect AWS integration. Focus on AssumeRoleWithWebIdentity events, which show successful and failed role assumption attempts with detailed error messages. Your external identity provider logs contain valuable debugging information about token generation and claim mapping issues. Set up CloudWatch alarms for failed authentication attempts to catch problems quickly. When troubleshooting OIDC authentication AWS issues, examine the JWT tokens your identity provider generates using online JWT decoders to verify claims match your AWS IAM identity provider expectations and trust policy conditions.
Security Best Practices and Optimization
Implementing least privilege access with granular permission sets
Start with minimal permissions and expand only when necessary. Create specific permission sets for different roles rather than broad administrative access. Use AWS Identity Center’s fine-grained controls to map user groups to precise resource permissions. Regularly review and remove unused permissions to maintain security posture. Document all permission assignments for audit trails and compliance requirements.
Setting up session duration and token refresh policies
Configure session timeouts based on security requirements and user experience needs. Set shorter durations for administrative access (1-2 hours) and longer periods for standard users (8-12 hours). Implement automatic token refresh to maintain seamless user experience while enforcing security policies. Monitor session patterns to optimize timeout values and reduce authentication friction.
Enabling multi-factor authentication and conditional access
Enforce MFA for all privileged accounts and sensitive resource access. Configure device-based conditional access policies that evaluate user location, device compliance, and risk scores. Set up adaptive authentication that triggers additional verification steps for unusual access patterns. Block access from untrusted networks or compromised devices automatically through AWS Identity Center’s security policies.
Regular auditing and compliance monitoring strategies
Establish automated monitoring for OpenID Connect AWS authentication events using CloudTrail and CloudWatch. Create alerts for failed authentication attempts, privilege escalations, and unusual access patterns. Schedule quarterly access reviews to validate user permissions and remove dormant accounts. Generate compliance reports showing authentication flows, permission changes, and security incidents for regulatory requirements.
Setting up OpenID Connect with AWS IAM and Identity Center might seem complex at first, but breaking it down into manageable steps makes the process much more approachable. You’ve learned how to connect your external identity provider to AWS services, configure the necessary trust relationships, and implement proper security controls. The key is taking your time with each configuration step and testing thoroughly along the way.
Remember that security should always be your top priority when implementing OIDC. Keep your token lifetimes reasonable, regularly audit your trust policies, and monitor your authentication logs for any unusual activity. Start with a small test environment before rolling out to production, and don’t hesitate to leverage AWS documentation and community resources when you run into challenges. With these fundamentals in place, you’ll have a solid foundation for managing user access across your AWS infrastructure.